This article is more than 1 year old
Chronos EZ430: An SDK packing watch for real techies
It's a timepiece, but not as we know it
The Windows software supplied will plot the accelerometer data onto pretty graphs, and even link motion to the Windows mouse-pointer. The hilarity of trying to control Windows whilst holding one's wrist steady enough to press the buttons (mapped to mouse clicks) was well worth the $50 alone - not only for the user attempting it, but also for colleagues and those passing by who might catch a glimpse of a frantically waving hand as the user misses the "Mouse Off" button yet again.
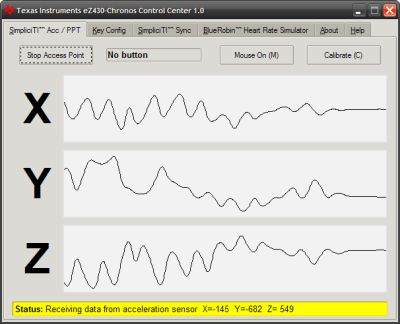
All that shaking is vigorous testing, not the result of a hangover
But hijinks aside it's the accelerometer mode which is most flexible, and what we used for our application.
Documentation is surprisingly sparse: there is a burgeoning community of developers and a good wiki, but for communications between the watch and the computer we were left with only the vaguest clues. The protocol isn't very complicated, though, and using HHD's Free Serial Port Monitor we were able to monitor communications with the watch and build a usable model of the communications process.
Having decided that what we really wanted was a music system controlled with a flick of the wrist - surely a common aspiration - we looked at the gathered logs and established that first we'd have to switch on the radio, then request updates, then poll for those updates every half second or so.
We used Java, because it was nearby, and opened up a serial port at 8 data bits, 1 stop bit and no parity, with a speed of 115200. Once open we sent a command to switch on the dongle:
0xff 0x20 0x07 0x00 0x00 0x00 0x00
To which we received a confirmation of success.
0xff 0x06 0x07 0xXX 0xXX 0xXX 0xXX
With "XX" being replaced with the serial number of our watch.
So we followed that with request to switch on the radio communications:
0xff 0x07 0x03
...to which we also, generally, received a confirmation:
0xff 0x06 0x03
But before we could start polling we had to run the preinstalled ACC application on the watch. Once that's running we can send a polling request and receive values for the X, Y and Z axis: one byte for each axis:
0xff 0x08 0x07 0x00 0x00 0x00 0x00
Which was rewarded with the data we're actually interested in...
0xff 0x06 0x07 0x01 0xc0 0x05 0xde
With the last three numbers being the attitude of the x, y and z sensors.
