This article is more than 1 year old
Trustpilot prunes florid iFlorist tributes
Weeds out suspect reviews
Following our look yesterday at some highly-suspect online reviews for iFlorist, Trustpilot has pruned a bunch of the offending tributes and is investigating the matter.
To recap, iFlorist was rated by many reviewers as pretty much the greatest website ever to grace the internet, which led us to question the authenticity of these outpourings of praise.
Our probe and iFlorist's reply to the allegations can be found here.
This morning, Julie Van Hemelryck, Trustpilot's Country Manager UK, got in touch to say:
Some of our clients pointed out the article you wrote on iFlorist. I have to admit that you are spot on, as we are in the process of investigating their reviews.
We always assume that a review on Trustpilot is a real one. Anyone on our site can report the review by clicking 'report abuse' under the review. Within 3 days, we look into the matter. In this case, I have asked 55 people for a proof of purchase to prove they are an actual customer from iFlorst. None replied, so I deleted all those reviews.
I also have to add that we are in touch with iFlorist, and discussing the matter with them too.
Here's iFlorist's current rating down at Trustpilot:
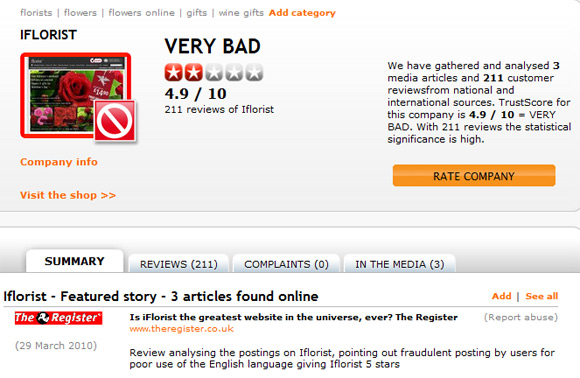
Suffice it to say, there are still a lot of dodgy-looking gushings awaiting the once-over by Trustpilot's veracity bureau, but we're gratified to see the matter is being addressed.
Finally, and in a quite fragrant twist to the tale, our original article this morning attracted the following comment from one "gef05", who was moved to protest: "You full of hate and criticism, but When need flowers who will call? iFlorist only place for beautiful flowers like dhalia, signifies the whisper of love between two people meant for one another."
Well done, sir. A lovely bunch of "dhalias" is as we speak winging its way to you in recognition of your unbiased and thoughtful opinion. ®
