This article is more than 1 year old
Why the Google antitrust complaint is not about Microsoft
It's about 'bundling' services with a search monopoly
Universal Google Product Search
But the filing's most compelling data concerns the price-comparison market. According to a Foundem study, more than 270 sample searches across what the Raffs call a broad sample of product- and price-comparison–related terms indicate that Google Product Search is far more likely to appear at the top of Google's search pages than competitors such as Shopping.com, Pricegrabber, Nextag, and the Raffs' own Foundem:
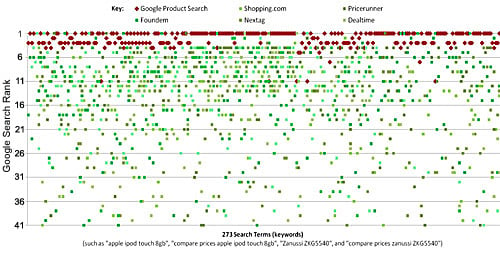
Google ranking of leading UK price comparison sites across a broad sample of product- and price-comparison-related search terms, as of 29 January 2010. Google Product Search results are shown in red. Other price comparison service results are shown in shades of green (source: Foundem)
What's more, according to a study that Foundem commissioned from comScore, the steep rise in the popularity of Google Product Search coincided with the introduction of Universal Search:
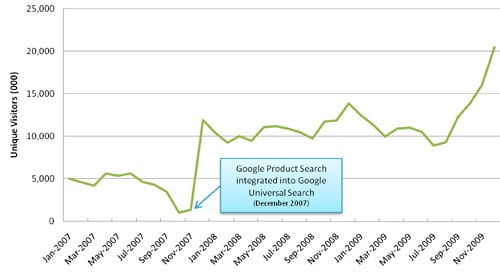
Unique monthly US visitors to Google Product Search between January 2007 and November 2009 (source: comScore)
The study also indicates that the rise of Google Product Search came at the expense of several Google competitors:
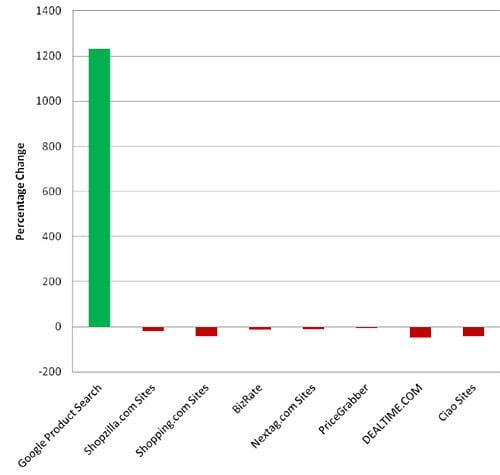
Percentage change in number of unique monthly visitors to US Price Comparison sites (including Google Product Search) from October 2007 to October 2009 (source: comScore)
The filing stops at the two examples: mapping and price comparison. But it warns that Google could apply Universal Search to, well, almost anything. "The two examples considered here illustrate the discriminatory market power of an overwhelmingly dominant search engine allowed to systematically favor its own services," it says.
"But these examples are just the tip of the iceberg. Similar harm to competition and innovation is inevitable when Google extends this strategy into new domains, such as financial search, travel search, property search, job search, social networking, browsers, operating systems, mobile, and so on."
