This article is more than 1 year old
Boffins peg co-polymers for cheap chip construction
Molecule lithography breakthrough
Scientists at the Massachusetts Institute of Technology have devised a potential chip-making technique that is the molecular equivalent of Doodles for Fun, a 1970s toy which kids used to make pictures by stretching coloured rubber bands on a pegged board.
The MIT team's pegs are silicon posts etched onto a chip using a standard, inexpensive photolithographic process of the kind used to create circuits in today's CPUs and GPUs.
The rubber bands are molecular co-polymers - two mutually repelling molecules which are nonetheless attached to each other, causing them to form specific shapes as they seek to get as far away from each other as possible.
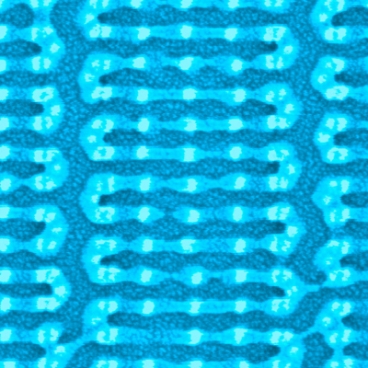
Pegs and bands: Molecules bonded to silicon posts
Source: Yeon Sik Jung and Joel Yang, MIT
This behaviour means scientists know exactly what patterns the molecules will form when deposited upon the silicon pegs.
The upshot, the team say, is the basis for a method by which complex circuitry can be marked out on a silicon wafer at sizes smaller than today's chip-making machines are able to work.
Currently, chip circuitry is created by covering the chip's surface in a photosensitive chemical which is then illuminated with light shone through a picture - called a 'mask' - of the connections and transistors. Where the light strikes, the chemical reacts, changing it into a substance that shields the silicon beneath it from the acid used to etch out the grooves that will be then filled to form the circuits.
The need to add more and more circuitry to a chip necessitates smaller and smaller wiring and components. That, in turn, requires ever lower wavelengths of light to be used. Soon chip makers will reach the point where they simply can't use light any more. New techniques will be needed to mark out the circuitry on the silicon.
Using molecules which are known to form specific patterns is one option. But previous research work has required grooves to etched in the surface of the silicon to form sites from which the polymers can assemble themselves.
Cutting the grooves requires expensive, complex electron-beam lithography. The MIT breakthrough is to find a way to create a framework - all those silicon pegs - in which the polymers can form the required shape using cheap photolithography.
The researchers' paper - "Complex self-assembled patterns using sparse commensurate templates with locally varying motifs" - is published this week in the journal Nature Nanotechnology.. ®
