This article is more than 1 year old
Game developer's lost electric buggy FOUND ON MOON
Vintage 1973 vehicle discovered by NASA orbiter
'Ivan, you fool, we're in a crater! Curse these imperialist photo maps!'
But then disaster struck. The Russian ground controllers, who handled the machine across a near-real-time link, accidentally drove it into a crater. As the machine struggled out again, it managed to get its heat radiator covered in Moon dirt. This dirt formed a strong insulator, causing the Lunokhod to suffer runaway overheating and wreck itself. The mission was abandoned.
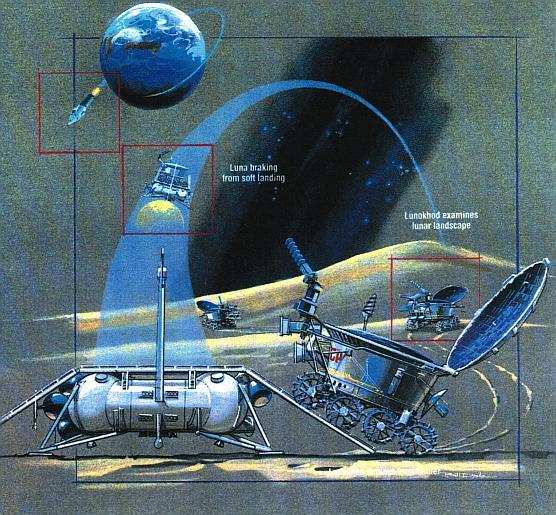
Glorious solar/nuclear moon-car technology of the 1970s.
The Moon not being mapped with great precision at that time, the exact final location of Lunokhod-2 has never been known. (The Lunokhod ground controllers actually had to use NASA Apollo-orbiter overhead photographs, cadged from America, to navigate.) The broken-down rover carries a laser-ranging reflector which can be picked out by precision ranging stations on Earth, but as this NASA pdf from 2002 tells us, laser ranging can't be used to pin the lost machine down on a Moon map:
The uneven distribution of accurate control points causes the accuracy of the network to vary strongly with lunar position. Future missions to the Moon could improve the accuracy ... Future lunar orbital missions should accurately map all of the Apollo sites plus the two Lunokhod sites plus any new lander locations.
