Even when it’s doing nothing, the Nexus One is visibly different from other handsets. Take the wallpapers that lie behind the homescreens - and Google has boosted the number of screens from three to five, though still not matching the seven available on HTC’s Sense user interface. Here you can choose animated wallpapers which respond to touch. Leaves floating lazily down a stream cause ripples when they bump, or you can ripple the water by touching the screen.
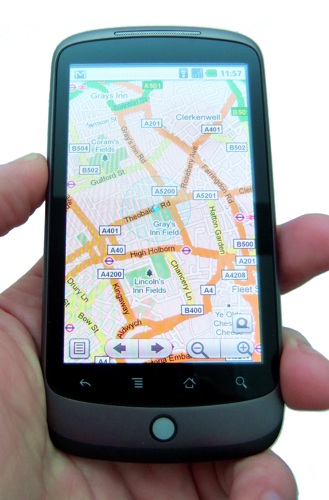
Google's usual Maps app comes pre-loaded
Other choices include an analogue sound meter and gently waving blades of grass. None of these will add to your battery’s performance, of course, but at least you can carry a spare with you. Take that, Apple!
The icons that work as program shortcuts are visually much improved since Android first launched over a year ago. The analogue clock is cuter, though the fact that there’s only one to choose from is an oversight. The applications list looks neat, with enhanced animations bringing it into view.
It’s easy to navigate between homescreens thanks to tiny rows of dots at the bottom corners of the display to indicate which one you’re on. Hold your finger on the dots and thumbnails of the main screens appear, to remind you just where you put the shortcut icon for the camera, for instance. You’ll need that shortcut, because there’s no physical camera button here.
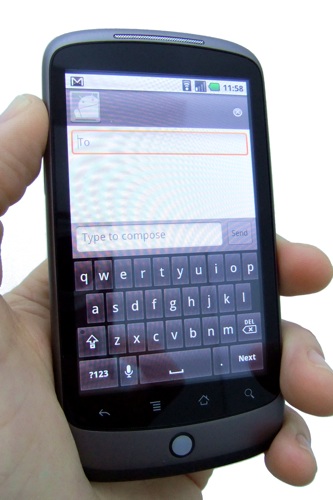
You'll have to make do with a virtual keyboard, but at least this one's very responsive
The 5Mp snapper here at least has a flash, but that doesn’t mean there’s no shutter lag – the perennial blight on mobile phone cameras. In fact, there’s a slight advantage to the lag here – touching the screen to shoot - or pressing the trackball - inevitably shakes the camera and the lag gives you half a second to still the phone. Results in reasonable light were effective enough, and Android makes is easy to send the images over Bluetooth, by email and multimedia message, and upload them to Facebook.
