This article is more than 1 year old
Tricorder/Aliens-motion-tracker handscanner kit gets $6m
3D air-bongo mouse shark tech in DARPA cashgasm
MIT air-bongo mouse will never do for Starfleet. Or DARPA
But existing kit, whether shark or MIT style, can't reach far from the detector. More range is required before Starfleet or the Colonial Marines would be interested.
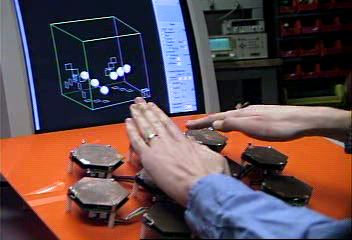
The electronic bongos were surprisingly difficult to master
Of course, once we're talking about transforming today's relatively humdrum US military into its possible science fiction successor, there's really only one agency to call. That is DARPA, the military research arm where they sneer at those who are merely on the bleeding edge: the edge where they live is so sharp that mere blood loss or severed limbs are nothing. If you weren't careful with it you might split atoms and start a devastating nuclear chain reaction in your own finger. An atom-splitting or fissioning edge, as it were.
And DARPA has answered the call of which we were speaking before we digressed slightly, announcing last week that it would shell out a cool $6,425,207 to Ohio tech house SRICO for a functioning E-FED.
According to the warboffins:
Electric field detectors are relatively large (especially at lower frequencies) so that compact detectors and arrays are not possible ...DARPA is seeking innovative research proposals for E-FED technologies that will enable the fabrication of dense detector arrays to achieve high spatial resolution of the electric field as well as high sensitivity.
Proposal solutions resulting in smaller and lower power sensors will be given preference to otherwise equally competitive proposals ... high sensitivity in a small form factor must be provided.
Full details on the E-FED project are avilable here in pdf: there are also some circuitry, code downloads and other tech details from MIT for interested garage Q-Branch enthusiasts here. ®
