This article is more than 1 year old
Argentinians invade Falkland Islands website
Sovereignty violated in Penguin News hack outrage
Argentinian hackers yesterday raised their national flag over the Falkland Islands' Penguin News - a temporary occupation in which they laid out their case for sovereignty over the South Atlantic paradise island group.
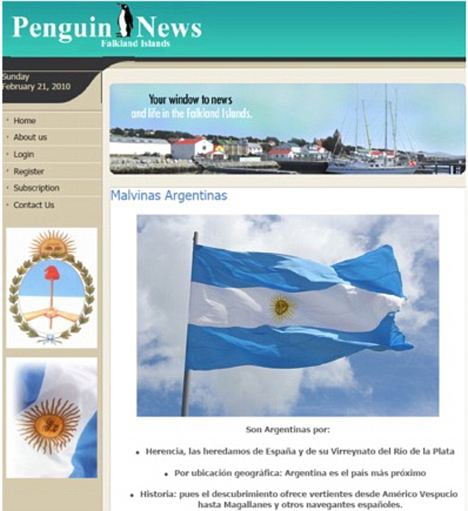
The invaders' bullet-point list of claims - backed by an rousing audio recording of the March of the Malvinas - suggested the islands are Argentinian because "they were inherited from Spain and its Viceroyalty of Rio de la Plata" and "because Argentina is the closest country".
These old chestnuts are, of course, completely at odds with the British position, which states that Las Malvinas are actually the Falkland Islands because we say so.
The hack comes as Britain and Argentina indulge in light sabre-rattling over the arrival of an oil rig which is set to exploit the liquid riches beyond the wildest dreams of avarice which lie beneath the remote outpost of Empire.
The Daily Mail explains that Buenos Aires "threatened to ban British companies with any links with the oil venture from the mainland, and has insisted that all ships travelling between Argentina and the Falklands must seek permission".
However, the Brit cruise liner Star Princess departed the Argentinian capital without hindrance, bearing 2,600 passengers set to step ashore at Port Stanley tomorrow "as one of the highlights of their South American cruise".*
Penguin News, meanwhile, had this morning lowered the Argentinian flag and was gamely battling on, despite the risk of sinking under an excess of bandwidth. ®
Bootnote
* Highlight? We dread to think what other destinations are on this particular cruise itinerary.
