This article is more than 1 year old
WIN a 500GB Wacko Jacko hard drive from Samsung
Man in the Mirror's movie pre-loaded
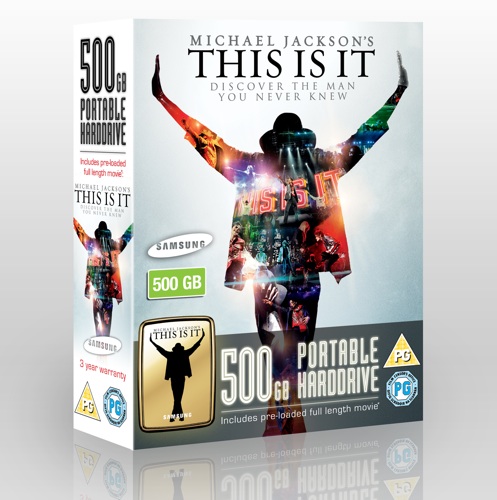
Competition Well, This is it. Yes, we're talking Samsung's latest 2.5in portable external hard drive, a gold-look model branded to tie in to the recently released Michael Jackson movie.
The Samsung drive packs in 500GB of raw storage capacity, is powered over the USB 2.0 bus and in addition to Sammy's usual excellent array of freebie back-up and data-encryption tools, comes with a copy of This is it pre-loaded on the drive for your viewing pleasure.
The Sony Pictures film is rated at PG, so Jacko's film is unsuitable for very young children.
And we have one of these stylish Samsung drives to give away.
To try and win the drive, all you have to do is answer the following three questions correctly, provide your full name and a valid email address. After the competition closes at Midnight, Friday 26 February 2010, the Reg Hardware randomiser will pick the winner from all the valid entries.
Entry to the competition is free. Sorry, but the competition is only open to readers resident in the UK aged 18 or above.
This competition has now closed.
Terms and Conditions
The Register Hardware Samsung This Is It HDD competition is open to all readers of Register Hardware resident in the UK aged 18 or over. No purchase is necessary to enter the competition. An internet connection is required to watch the pre-loaded movie.
The Competition is not open to employees of Samsung, Situation Publishing Ltd, their families or agents. Multiple entries will be disqualified. Only one entry is permitted per household. No cash alternatives will be offered. The prize is subject to availability and if, due to circumstances beyond Register Hardware's control, we are unable to provide the stated prize, an alternative prize of equivalent value will be supplied. Register Hardware will not be liable if the prize does not reach the winner for reasons beyond our control, or if the prize is damaged during delivery.
Each entrant must supply a valid email address to which a confirmation email will be sent should the entrant's name be drawn. The winner will be the first name drawn from entrants who have correctly answered the questions posed. Winners will be notified by email within 28 days of the closing date, and must respond within one week. Winners who do not respond within this time may be disqualified and another winner drawn in their place. The editor's decision is final, and no correspondence will be entered into. Closing date: Midnight, Friday, 26 February 2010.
By entering the competition you agree to have your supplied personal details passed to the sponsor so that they can contact you with further information about their company, products and services. ®
