This article is more than 1 year old
Climategate witchhunt fingers scientist
Police quiz tests the faith
Police have questioned a scientist at the University of East Anglia in connection with the leak of emails from the University's Climatic Research Unit.
Paul Dennis, Head of Stable Isotope and Noble Gas Geochemistry Laboratories at UEA, has produced studies in support of Global Warming, but this didn't stop him falling under the Inquisitors's suspicion. Police told The Guardian that Dennis had been questioned.
Like witches in the old days, Dennis had apparently shown signs of aberrant or 'denialist' behaviour. He reportedly refused to sign a petition in support of disgraced CRU director Phil Jones, and had communicated with Lucifer Canadian statistician Steve McIntyre, who over the years has uncovered malpractice amongst the High Priests of Paleoclimatology. One of the Priesthood, NASA's Gavin Schmidt and Real Climate blog, tipped the wink to UK Police.
The existence of the archive was known at Climate Audit, Air Vent, and Watts Up With That, two days before the story broke, and the bloggers rubbished the suggestion Dennis was the source. Dennis only made his enquiry after the story broke. Dennis himself denied involvement in this comment at Bishop Hill blog.
"The police had copies of my email correspondence with Steve McIntyre and Jeff Id and a copy of my paper which kind of amused me. They said it was because I had sent the emails that they were interviewing me. I have absolutely no problems with that," he wrote.
How to find a witch
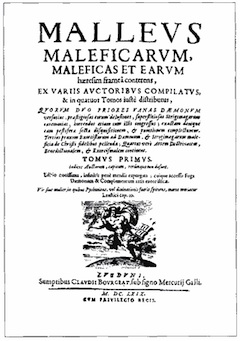
Yet if there is to be an 21st Century update to the Malleus Maleficarum, or Witchfinder's Manual, then the Police are well on the way to writing it*. Investigators looking into the CRU breach are sending out a 21-question survey to people who may help with their enquiries. It begins innocently enough:
2) ARE YOU EMPLOYED / FUNDED BY ORGANISATION/ PERSON
YES / NO
3) ARE YOU A MEMBER OF ANY PROFESSIONAL ORGANISATIONS
YES / NO
4) DO YOU HAVE ACCESS TO A USER ACCOUNT AT UEA?
Having taken some time, by the middle of the questionnaire, Plod is going right for the jugular:
12) WHAT / WHO WAS SOURCE OF INFORMATION?
If the culprit still hasn't confessed, the final questions may help.
18) WHAT IS YOUR STANCE ON CLIMATE CHANGE?
19) ARE YOU A CURRENT OR PAST MEMBER OF ANY POLITICAL OR ENVIRONMENTAL ORGANISATION / GROUP?
YES / NO
20) DO YOU CONTRIBUTE TO, PARTICIPATE IN, OR ADMINISTER ANY INTERNET BASED WEBSITE, FORUM, BLOG, ETC. INCLUDING ANY RELATED TO CLIMATE CHANGE?
YES/NO
There are simpler methods. Ducking stools should suffice. If the accused "denier" floats, he's guilty. But if he drowns, we can pronounce him guilty upon his death. Sorted. ®
* Thanks to Bishop Hill for the tip.
