This article is more than 1 year old
CA taps IBM alum as chief exec
McCracken takes the helm
CA has tapped another IBM veteran as its next chief executive officer, replacing its turn-around champion John Swainson, who retired from the IT management omnicorp's helm at the close of 2009.
The company's new CEO, William McCracken, has served as executive chairman since Swainson's retirement plans were announced in September. Both men had spent about three decades working under Big Blue before joining CA's ranks.
Under McCracken's lead, CA plans to spend at least $300m per year on "cloud computing" and security software acquisitions in order to better compete with rivals Oracle and IBM, the new CEO told Bloomberg. He now holds both the CEO and chairman of the board positions at CA.
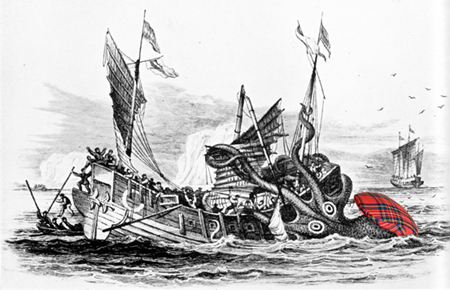
William McCracken (artist's representation)
McCracken left IBM in 2001 as general manager of the printing division. He previously served as IBM's EMA and Asia PC company and general manager of marketing for IBM's PC market.
Swainson took over as boss of CA (then-Computer Associates) in February 2005 after his predecessor, Sanjay Kumar, was charged with fraud, conspiracy and obstruction of justice over a $2.2bn hole in the company's accounts. The company was rebranded under the initials CA in a move to distance itself from its troubled past.
CA appears to be financially ship-shape now as McCracken takes the chair. In its third quarter earnings announced on Thursday, CA reported $1.13bn in revenue, up 8 per cent compared with last year. Net income was $257m, a 24 per cent jump year-over-year. ®
