This article is more than 1 year old
Panasonic intros compact camera foursome
The sexy shooter, the tough guy, the ultra-portable and the cheapskate
Panasonic has kicked off 2010 by refreshing its compact camera line-up, launching four models to cater for everyone from first-time shooters to photography feature fanatics.
TZ10
The Lumix DMC-TZ10 included all the usual shooting features – such as face detection, geo-tagging and 720p video capture – you'd expect on such a high-end compact.
Sew these features together with 12.1 effective megapixels, a 12x optical zoom and body with a 3in LCD and you have a camera that Panasonic will gladly push your way come mid-March. A price hasn’t been confirmed.

FT2
Also available come mid-March will be the new FT2, which Panasonic will target at outdoor types. The camera is waterproof to 10m, shockproof to 2m, freezeproof to -10° - and dustproof to boot.
Capture 14.1Mp stills using the FT2’s still photography mode or switch to video capture and you can bag 720p mini-movies of friends and family.
The FT2’s other notable features include optical image stabilisation.

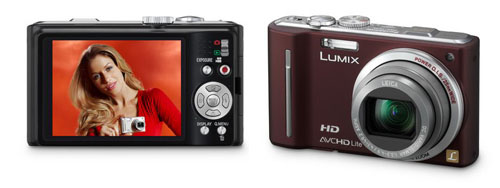
TZ8
The TZ8 has a 12x optical zoom and 14.5Mp sensor. Like the others, it too supports 720p video capture and also features manual controls for “advanced expressive shooting” – including aperture and shutter controls.
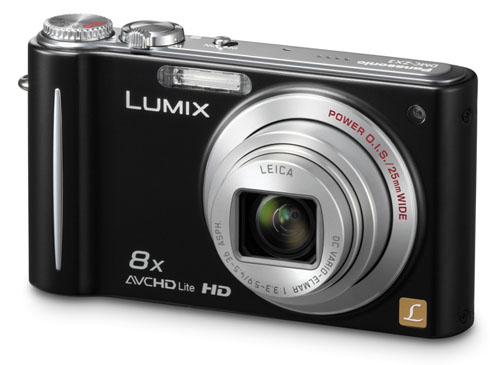
ZX3
Finally, the ZX3 is Panasonic’s successor to the established ZX1.
The new model combines a 14.1Mp sensor and a 25mm wide-angle lens with 8x optical zoom and 720p video capture.
We were a little put off by the ZX3’s small-ish, 2.7in display, but the camera still features all the standard photography tools, including face detection, a whopping 28 pre-set still scene modes and a further 18 modes for video capture.
All four Panasonic compact cameras will be available in Blighty come mid-March, and in various body colours. The company hasn’t released any prices. ®
