This article is more than 1 year old
Keene IRAnywhere
IR over IP – for those remote remotes
Review Infrared remotes are easily taken for granted for controlling the TV from the couch, but with the Keene IRAnywhere system, you can take channel hopping to the next level. Ever wanted to change the channel from across international borders? For long-distance disciplinarian dads, the possibilities for family fun are endless.

Couch potatoes go global with Keene's IRAnywhere
OK, so that’s not really what it’s for, but the Keene IRAnywhere system (KIRA) will relay IR signals over any local network and, with the use of a service such as No-IP.com or DynDNS.com, this functionality can be extended using the Internet.
The KIRA package includes two 60 x 60 x 28mm receiver/emitter modules with a power supply each and just one IR ‘wand’. The modules feature an Ethernet port, a built in IR receiver, an input for an external IR receiver, various status LEDs, a reset button and an output for an external IR emiiter, such as the wand.
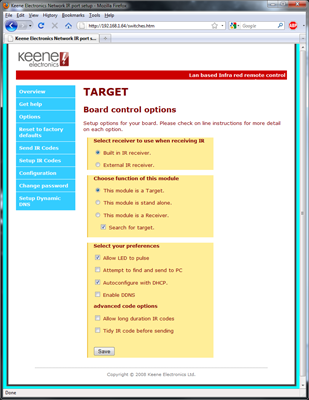
In standard operation mode, the target (emitter) and receiver units are hooked up to a network using their Ethernet ports. Each KIRA can be configured from a web browser to operate as a receiver, a target or as a standalone device.
With a typical a pairing, the receiver simply relays the signals it receives to the target module, which then broadcasts the signal out to any present IR equipment. It is possible to operate multiple receivers and targets on the same network, and, providing they are configured correctly, multiple receivers can transmit to a single target.
KIRA comes preconfigured to use DHCP and searches for other devices on the network. Each module is already preset to form a target and receiver pair, so it’s literally plug in and hit play – on your remote. Still, if this is not what you had in mind, the modules can easily be tweaked to your liking using the browser’s simple, yet powerful configuration interface.