This article is more than 1 year old
Buffalo Linkstation Duo
The paperless office stationery cupboard?
The use of gigabit Ethernet is now standard across most decent Nas devices and its benefit is certainly observable with the Linkstation Duo, with read speeds exceeding 30MB/s.
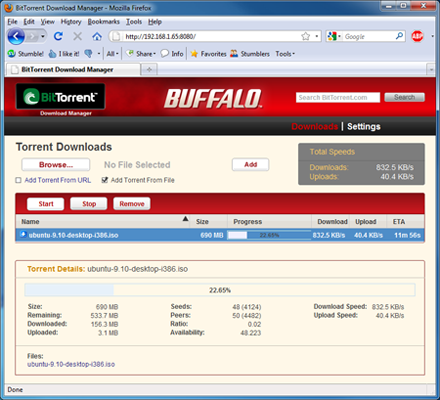
The obligatory BitTorrent client
It’s likely most home users will be relying on networking gear supplied as part of an ISP’s package that runs at 100Mb/s and will need to consider options such as a decent gigabit router or use a gigabit switch as part of their LAN to make the most of their purchase.
The USB port utilises Buffalo’s Direct Copy feature, which copies data from a USB device to the Linkstation, as well as providing print server functionality. This feature works well, but only copies common media file types. With this in mind, it’s far from ideal to be used to as a backup mechanism for general data but is intended mainly as a quick and easy way to backup music, video and photos.
Just be aware that the Linkstation will disconnect from the network when USB devices are added and removed, which may cause interruption to other tasks. Regarding backups, Buffalo even allows scheduled backups to other Buffalo network storage devices or attached USB drives.
During operation, the device runs cool and quiet with the rear fan never rising above a whisper. The use of Samsung EcoGreen drives also means that vibration is minimal to the point that it would only be noticed if it was placed in your immediate work area. Power consumption is also minimal, with the Linkstation Duo drawing approximately 12W at idle and with a high of 24W recorded under load.
Data Read and Write Test Results
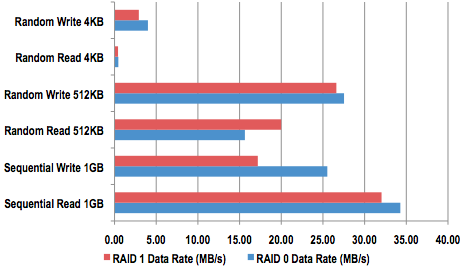
Longer bars are better
Our tests revealed that the claimed data rate of 40MB/s is close to real-life when reading large files. Indeed, whilst it’s certainly not the fastest Nas out there, the Linkstation Duo has sufficient throughput to handle most home and small office applications with ease.
