This article is more than 1 year old
Facebook urges public exposure in 'privacy' revision
Share everything, please
Facebook is urging its 350 million users to open their kimonos to the entire internet as part of its revamped security settings.
Unveiled on Wednesday, the social network's new privacy controls are designed are to expose a user's personal data - including status updates, posted content, and details about friends and family - to everyone on the wild, wild web.
Facebook says the freely-shared data "makes it easier for people to find and learn about you" — but critics claim it's a actually ploy to drive up Facebook traffic by getting more of its pages cataloged by RSS feeds and search engines.
Starting now, when a current user logs into Facebook, they will be asked to review and update their privacy settings. Users are then prompted to make changes to who (and what) is allowed to ogle various sections of their profile and postings.
While Facebook allows users to retain their old settings quite easily, the recommended options strongly encourage a brave new world of personal data sharing:
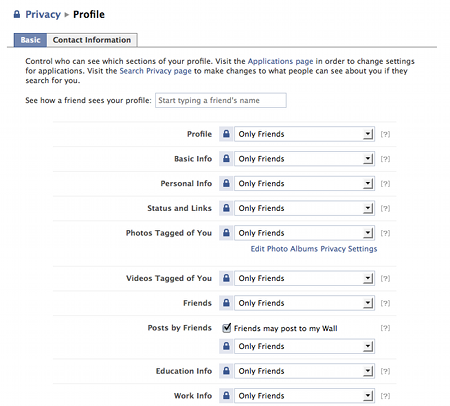
From this...
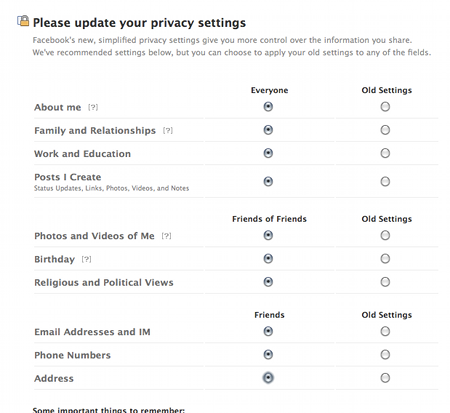
Facebook recommends this.
It should be noted that users under 18 are restricted to sharing details with Facebook friends no matter which options they select.
Conspiracy or innocent silly buggers? Hard to tell. Facebook, after all, is the king of empty gestures and policy changes to keep critics off its back. ®
