This article is more than 1 year old
Acer Aspire 1810TZ
Small laptop, enormous battery life
The reason the keyboard is so far forward is that the battery takes up a large part of the back end of the 1810TZ's body. But that's a good thing, because it's a six-cell 5600mAh job so it can hold a charge for a good, long run.

The trackpad is a bit on the small side, but does do multi-touch
And it's well integrated into the 1810TZ's design, unlike some six-cell netbook batteries that jut out well beyond the lines of the laptop. Apart from a shallow bulge on the bottom of the machine, you wouldn't think this notebook had such a capacious power pack.
Speaking of the base, Acer has provided hatches for the 250GB Sata hard drive, the memory - two slots, both populated, alas - and the Wi-Fi card. Acer isn't currently selling a 3G-enabled 1810TZ in the UK, so while there is a SIM slot under the battery, there's no 3G card. Don't expect to be able to add one: there's space for it, but Acer hasn't fitted the secondary Mini PCI slot it would need, or the antenna cables. There's no Bluetooth, either.
But back to battery life. We took the 1810TZ to a conference, turned off Wi-Fi and nudged the display brightness down to its still-well-illuminated minimum and Windows reported we had well over eleven-and-a-half hours' runtime. And the battery wasn't even full.
Acer claims the Timeline series delivers over eight hours' battery life, and we can well believe it. Looping PCMark Vantage yielded a runtime of over four hours: 258 minutes, to be precise.
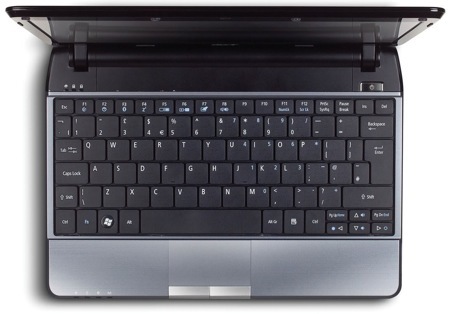
The keyboard's good to use
This is an extreme test designed to allow us to compare different laptop batteries properly, so don't expect a real-world runtime as low as this. We estimate you'll get around double this time using the Aspire for typical notebook browsing, email and productivity duties, so Acer's claim is right on the money.
