This article is more than 1 year old
Kingston SSD Now V 40GB boot drive
Game changer?
We tested the Kingston drive on an Intel Core i7 870 system and saw these figures were accurately reflected when we ran HD Tach 3 and CrystalDiskMark 2.2 benchmarks. The time taken to copy a 2GB folder of files within the 40GB SSD was many times slower than the 80GB and 160GB Intel X25-M drives.
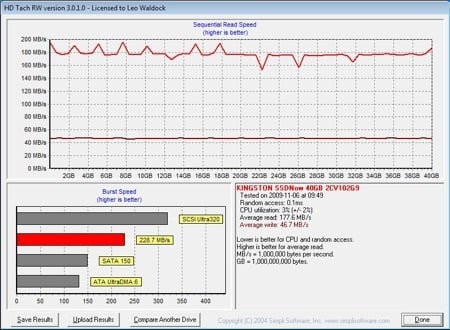
Iometer shows a brighter side to the story as the read performance of the Kingston is very similar to the 160GB Intel drive, although write performance once again shows up as significantly lower. This makes sense as the hardware is very similar in both drives except that the Kingston drive uses fewer Flash chips.
The important point is that Kingston delivers on read performance and that’s exactly what you need when you’re starting Windows or loading an application off the disk and into memory.
The matter of the 40GB capacity is somewhat vexed. You need to allow 20GB for an installation of Windows 7 so you’ll have to work damn hard to get your boot drive down to 40GB unless you’re happy installing applications to a secondary drive. Provided you can handle the discipline of uninstalling unwanted application and games, we predict that the Kingston will make massive inroads into the desktop market.
But what we really want is a cheap 80GB SSD as that would make life much easier.
Verdict
 Kingston has delivered a disguised Intel X25-M that will transform your PC for a trivial amount of cash. ®
Kingston has delivered a disguised Intel X25-M that will transform your PC for a trivial amount of cash. ®
More SSD Reviews...

Intel X-25M |

Crucial CT256M225 |

Patriot Torqx |

OCZ Vertex |

