This article is more than 1 year old
Nokia 6303 Classic
A no-frills phone just for talking on? Surely not?
Review While Nokia continues to push at the boundaries of mobile phone technology, it also has its eye on the voice-as-primary-function mainstream. This is where its bread and butter lies, and a market well served by the stalwart and very popular 6300. Now meet its successor, the 6303 Classic.
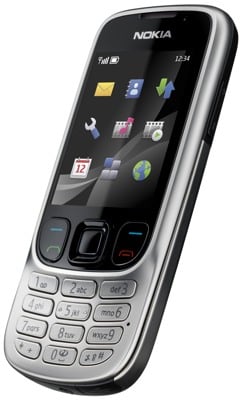
Nokia's 6303 Classic: the candybar handset that wants to be a slider
As such, it's a handset with few frills. There’s no GPS, no Wi-Fi and no 3G. Actually, 3G is one absence that that may hold this handset back. What constitutes the mid-range is moot, but for our money 3G is one feature that's fast becoming, if it isn't already, a must have for all but the most bottom-of-the-ladder phones.
Incidentally, if you want 3G - and also GPS and a better camera - then maybe the £200-plus 6700 Classic might be more up your street.
Back to the 6303 Classic and it's a candybar handset with a very teensy twist. The size and weight are well within acceptable parameters - 108.8 x 46.2 x 11.7mm and 96g - but what's unusual here is the way the screen and shortcut buttons are enclosed in a frame which is curved and raised up from the number pad.
As you can see from the pictures, it makes it look like an open sliderphone. It doesn't slide but it is distinctive, and fortunately doesn't impede how you use the phone. The number keys have been squeezed a bit to make room for the relatively large rocker keys either side of the navpad. These combine Call and End with the soft-menu buttons.
However, the number keys themselves are well separated from each other and are tactile. The bottom row is close to the edge of the handset, though, and the outer keys are almost half the size of the other buttons because of the curve of the handset's base.

The number keys aren't bad, but the bottom row keys can be tricky to tap
The build quality is good for a phone at this price point. There's enough metal in the chassis to make the handset feel substantial and to allow it to take a few knocks and drops.
