This article is more than 1 year old
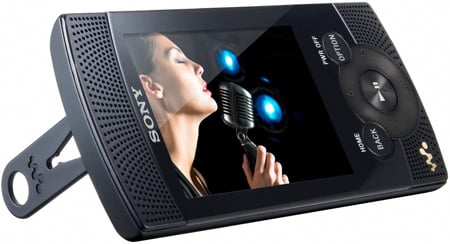
Sony Walkman NWZ-S544
PMP with speakers, anyone?
Review Do pocket media players need built in speakers? Certainly, apart from the Touch, Apple doesn't seem to think so and let's face it, love it or loathe it, Apple knows a thing or two about selling MP3 players to world+dog.

Sonic boon? Sony's Walkman NWZ-S544
Sony, however, begs to differ and has launched a new series of Walkman players complete with built-in stereo speakers. A stroke of genius, or a niche too far? Physically, the new S class resembles a slightly stretched version of the E-class player we looked at last month.
Happily the installation of two small speakers at the top and bottom hasn't done too much to increase the size of the device which, at 49.3 x 99.3 x 10.2mm and 68g, remains reasonably light and compact despite having a 2.4in, 240 x 320 display, rather than the E's 2in affair.
External controls are the now familiar Walkman norm, the only major difference being the addition of a rocker to switch the speakers on and off. The speakers, which face both forward and back, are mounted on the left hand side of the player at both the top and bottom. They are concealed by robust grilles, which bode well for the device's longevity.
To give the front and back speakers the best chance, Sony supplies a plastic clip-on stand that props the 544 up at around 80° and puts the speakers at the 'top'. The problem with the stand is that it is a wretched flimsy plastic affair that, almost certainly within days of purchase will either snap or be mislaid.
Making a stand
Technical details of the speakers are a bit thin on the ground. All Sony will say is that they are Digital Linear Phase Speakers that incorporate Linear Phase Correction and have Virtual Bass, all of which sounds rather impressive.
