This article is more than 1 year old
Freecom Secure
Swipe your card, gain access to your external HDD
Likewise, touching the front with a smartcard will also unmount the drive.
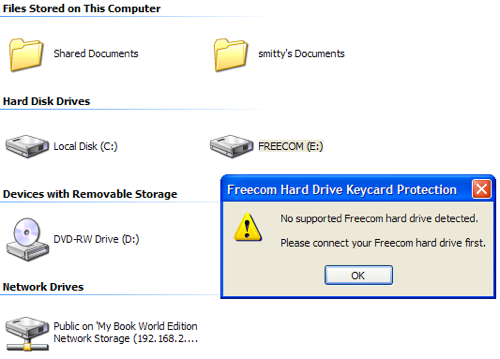
In that sense, it works, but of course there's no way now to, say, remove the protection facility, which the utility allows, or register extra cards if you lose one. The bundled software lets you carry out both these tasks.
Whoops
The Hard Drive Secure can remember only two cards at once, by the way, so if you want the one drive to be accessed by more than two users, it means sharing cards. In fact, one card is intended to be a 'master' card kept safe in case you lose the other one. So this is really a one-user product.
It's also worth noting that while the system worked enough to allow us to enrol the cards using Windows, the Mac software never saw the drive. We're using Snow Leopard, and we suspect Freecom's software may not be compatible, though there's no appropriate update on the company's website yet. The command line script that kicks off the Mac installer failed with a 'Cannot Execute Binary' error. No surprising, that, since it's a PowerPC binary. Has Freecom not heard that Apple has gone Intel?
Despite all this, the drive worked on our Mac, because the security system lies within the Hard Drive Secure itself. But it's a problem if you need to re-configure it and don't have a PC handy.
Back to the drive, and the smartcard sensor works quickly. The sensor is in the centre of the drive's front panel, but the cards' RFID chip is not centred, so it's possible to place one half of the card over the sensor and the sensor won't 'see' the chip. It works best when the whole card is placed flat against the drive.

Enrol your cards
The smaller of the two LEDs on the front tells you if the drive is locked or not - the other indicates the drive is powered up - and again, it's best to look at it straight on. At too sharp an angle between drive face and line of sight you can't quite see what the colour is. This doesn't matter too much in use, but it does when you're trying to enrol your smartcards.
