This article is more than 1 year old
Idle wild: how Intel's mobile Core i7 speeds up to slow down
Turbo Boost, Thread Parking and the drive for low-power performance
Intel's first mobile Core i7 processors - codenamed 'Clarksfield' - incorporate a feature the chip company is calling Turbo Boost. It's not new - the technology is a part of every 'Nehalem' architecture-based CPU the company has released to date.
So, Turbo Boost can be found in desktop chips and it's in Xeon server parts too. But it really comes into its own in processors produced for laptops.
Intel's Clarksfield: all four cores can be powered down to zero
The mobile Core i7s are all quad-core parts, and while model numbers and operating clock frequencies differ, Turbo Boost works the same way in each case. The technology takes feedback from on-chip thermal sensor and watches how the operating system is scheduling work on the available cores. Using both sources, Turbo Boost sees if it can lift the chip's clock speed and operating voltage above baseline.
A 2GHz chip with threads scheduled on all four cores has the scope to be dynamically overclocked up to 2.26GHz, provided there's room within the chip's thermal envelope to do so. That's 55W on the 2GHz Core i7-920XM, falling to 45W with the 1.73GHz i7-820QM and the 1.6GHz i7-720QM.
If an application is only making use of two of the four cores, the remaining pair of processing units can be powered right down to zero, dropping the chip's overall thermal output and allowing the two running cores to be clocked anywhere up to 3.06GHz.
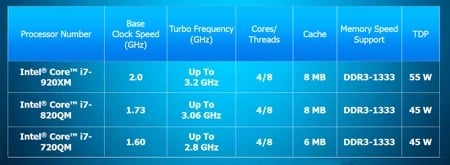
The current Clarksfield line-up
A one-thread, one-core application presents even more room for lifting the clock frequency as the other three cores are sent to deep sleep, slashing the heat coming off them and, in turn, allowing Turbo Boost to up the one core's clock frequency up to 3.2GHz - 60 per cent higher than the stock clock speed.
