This article is more than 1 year old
Fujitsu M2010 netbook
Shiny and solid, but still needs polish
Given the 2cm of glossy black nothingness above the keyboard and 1cm edging either side, Fujitsu could have made better use of the available space. With bit of careful design there’s no reason why a 10.1in netbook’s keyboard has to be fiddly – the recently-reviewed Samsung N110 is testament to this, with its keyboard stretching right to the very edges of the chassis.
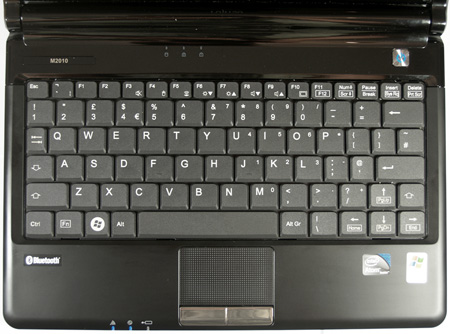
Given all that plastic surround, the keyboard really should have been taller and wider
A few oddities have also crept in on the keyboard, most notably the right Shift key being squashed and placed just above the right arrow key. The F12 key is another victim and has to make do with sharing its spot on the keyboard with the F11 key, while the ‘1’ key’s placement at the very edge of the top row also caused problems – we frequently hit the ‘2’ key by accident. There is also noticeable flexing on the right side of the keyboard.
It’s not all bad news, though. The Ctrl and Fn keys are the right way round and the arrow keys haven’t been slimmed down, while all keys feature a decent amount of travel and spring back into position nicely.
The trackpad measures 54mm by 33mm and responds well, but we're certainly not fans of the two buttons below it. Emitting a loud clacking noise each time you depress one, it's something that could drive fellow commuters, family members or anyone else in the near vicinity to tear it from your hands and hurl it out of the window.
A quick journey around the M2010 unearths the usual selection of netbook ports. VGA-out and a single USB port are located on the left side, while over on the right audio in/out and a memory card reader are joined by a further two USB ports and a 10/100Mbps Lan port.

Percussion pads? A loud ‘clack’ greets each trackpad button press
The fan, which belches hot air out of the left side of the chassis, regularly fired up during testing. Only when it ramped up to full speed did it become annoying but, thankfully, this only occurred a few times when we were being particularly harsh on the M2010.
