This article is more than 1 year old
Inside Intel's 'Moorestown'
Can Atom 2.0 get into smartphones?
Intel claims that, on average, Moorestown will consume less than half the power that Menlow does, but the real boost comes to the amount of power it uses up while on stand-by - one fiftieth of Menlow's idle power consumption, the company claims.
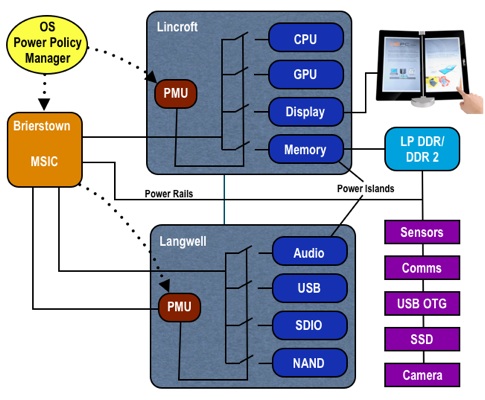
Moorestown's 'fine-grain' power management
Menlow consumes 1.6W in stand-by, putting Moorestown at around 32mW.
That, Intel hopes, will be sufficient to allow, say, a high-end smartphone to run for a day or two between charges, depending on usage.
The level of stand-by power consumption is central to Moorestown's design philosophy. And it's not only about keeping the power loss right down while the host device isn't doing anything. Moorestown was also designed to get as much work done in as little time as possible in order to get the device back into that ultra-low power idle state as soon as it can.
Lincroft's contribution to that is manifold. The CPU core, which is essentially an existing 'Silverthorne' Atom, is accompanied in the package by a 2D/3D graphics engine, a memory controller, a video decoder and encoder, and the display controller.
All of these components are managed by an on-chip Power Management Unit (PMU) that can completely switch off any of them that aren't being used at a given moment. Moorestown uses pre-programmed power usage policies that govern what gets switched off and when. If the handset's screen is off, for example, the display controller, video and graphics engines can be powered down.
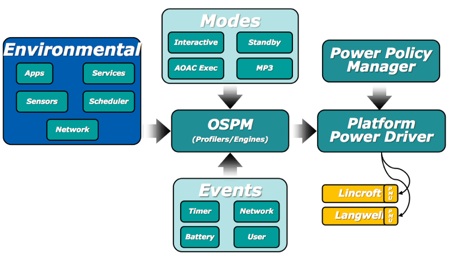
Moorestown's power management systems' interplay
If you're listening to music, off goes the CPU too while Langwell's audio engine handles the work. Alongside that component, Langwell is home to Moorestown's embedded, SDIO, USB, NAND Flash - ie. storage - and camera controllers. There's no PCI Express - that's too PC-centric and not needed here, says Intel, though it will be a part of Pine Trail's 'Tiger Point' I/O chip - with all other peripherals, such as Intel's own Wi-Fi, Bluetooth and GPS module, 'Evans Peak', connecting over the SDIO bus. Intel has added a CE-ATA bus too, presumably with an eye on set-top box opportunites.
While Lincroft is fabbed at 45nm, Langwell is a 65nm part, though their packages are effectively identical in size.
