This article is more than 1 year old
Inside Intel's 'Moorestown'
Can Atom 2.0 get into smartphones?
Pulling the graphics core from the chipset into Lincroft doubles the 2D and 3D performance, the chip maker claims, while reducing power consumption. Again, that's by reducing the need for expensive - in power terms - CPU cycles.
The graphics core will support not only OpenGL ES 2.0 but also OpenVG 1.0, the vector graphics acceleration API.
Other design choices will help device makers reduce power consumption further. For example, Lincroft's display controller supports the LVDS (Low-Voltage Differential Signalling) used to run most of today's notebook screens. But it also supports the newer MIPI (Mobile Industry Processor Interface) Display Serial Interface bus, which consumes 125mW less than LVDS.
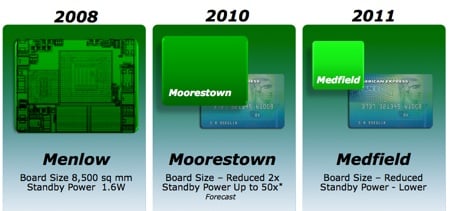
Honey, I shrank the chips
Likewise, while Lincroft's memory controller will support DDR 2 - for PC-style devices, says Intel, even though it's removed other PC-centric technologies from the platform - it also supports low-voltage DDR memory for better power consumption. In both cases, memory connects over a single channel.
Intel has admitted that its figures for Moorestown's power advantage over Menlow assume the use of MIPI-connected peripherals - the camera controller uses the same bus technology - so vendors who use LVDS displays won't be allowing Moorestown to do its best to conserve power. But LVDS has to be there because of the sheer number of LVDS screens on the market and the paucity of MIPI devices.
And it has said that Flash content playback will still be handled by the CPU, which could hit battery life hard given how many websites rely on Flash. This is one reason why Flash is absent from the iPhone, and may come to bite Intel - always keen to stress how Flash friendly its platforms are - hard.
Real-world usage will be the real test of Intel's claims for Moorestown. Unfortunately, we have a long wait before we can see how well Intel's design team has met the challenge. ®
