This article is more than 1 year old
Inside Intel's 'Moorestown'
Can Atom 2.0 get into smartphones?
That's why Lincroft has special video decode and encoding engine. Previous platforms left that kind of task to the CPU, but the dedicated circuitry and perform the same task with less of a strain on the battery, allowing the CPU to be kept powered down.
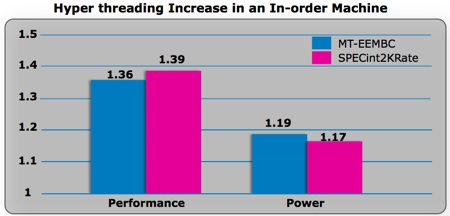
HyperThreading advantage: performance gain outweighs rising power draw
Figures relative to normalised single-core scores
Moorestown also has Bus Turbo mode that follows the CPU core burst mode to up the memory bus frequency in order to reduce latency to get data to the processor as fast as possible, again making for a more speedy completion of the task at hand.
Dozens of usage scenarios inform the power management polices that govern what elements Moorestown can safely switch off at any given moment. If the CPU core can't be shut down, the power management system aggressively targets the lowest possible clock frequency and voltage combination that it can get away with.
How well it will work in the real world remains to be seen - Moorestown won't ship until mid-2010, and devices based upon it won't be available for the best part of a year from now - but compared to Menlow, the power savings are significant, intel claims.
Playing a 720p HD video on a Moorestown consumes a third of the power it does on Menlow. Video playback does require a little CPU work - audio playback doesn't and here the power reduction is a whopping 25-fold. Intel hasn't published actual mW figures, but its comparison chart (above) shows Moorestown's music power demand is tiny compared to Menlow's.
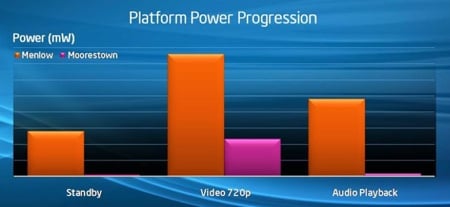
Power savings: Moorestown vs Menlow
In addition to burst mode, Lincroft's CPU once again has HyperThreading, allowing the OS to schedule an extra thread to run in parallel with the current one, if the necessary CPU resources are available.
