This article is more than 1 year old
PC tune-up software: does it really work?
Part One: Windows XP
All the ‘one-click’ performance optimisations, registry fixers and registry defraggers were enabled followed by two restarts before testing began.
Operating system start-up time is undoubtedly the most important aspect of computer speed for many users. We didn’t expect the Ram upgrade to have an impact here, since the hard drive is what is doing most of the work but, surprise surprise, it shaved 23 seconds off the start-up time.
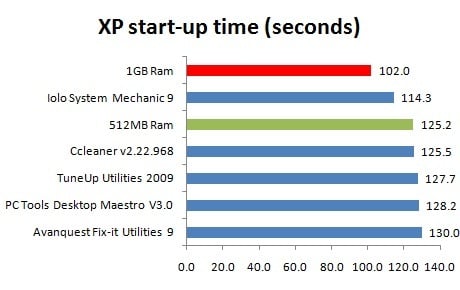
The Ram upgrade and Iolo System Mechanic lead the way
Shorter bars are better
As we’ll explain later, Iolo System Mechanic 9 originally booted up a lot faster but we had to re-enable some of the services it had disabled to ensure a fairer test. Nevertheless, it still improved boot-up time by 11 seconds.
PC Tools Desktop Maestro and Avanquest Fix-it Utilities both load up their applications during startup, which is potentially why they’re a bit slower than a stock system. We found start-up time could be improved by around 18 seconds when using the tune-up applications’ start-up managers. This meant we could disable 12 different applications we weren’t using, including a couple of old wireless utilities, a toolbar, a faxing application and Java updater.
We decided to side-step traditional synthetic benchmarks like PCMark in order to get as close to real PC use as possible. The DMS Clarity Studio puts Microsoft Office through its paces by timing how long it takes to perform a series of tasks in Word, Excel and PowerPoint. Print jobs are processed, text is formatted, and pages are scrolled up and down in this formidable test.
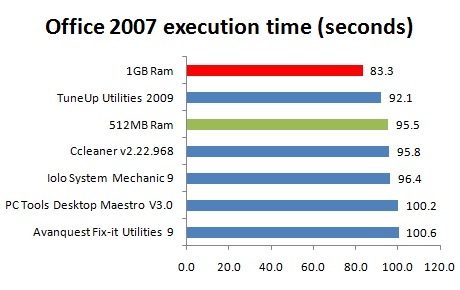
The Ram upgrade did the business here, although TuneUp Utilities did a good job too
Shorter bars are better
The Ram upgrade won again, while TuneUp Utilities 2009 also managed to speed up Office response time. PC Tools Desktop Maestro and Avanquest Fix-it Utilities both managed to reduce Office performance by a small margin.
