This article is more than 1 year old
LaCie LaCinema Black MAX
Stylish media streamer and DVR combo
The device makes a good impression when you turn it on for the first time – it was able to quickly scan for TV channels and to automatically connect itself to our network without throwing any confusing network settings at us. The unit’s internal fan makes more noise than our Sky+ box, but wasn’t loud enough to become annoying or obtrusive.
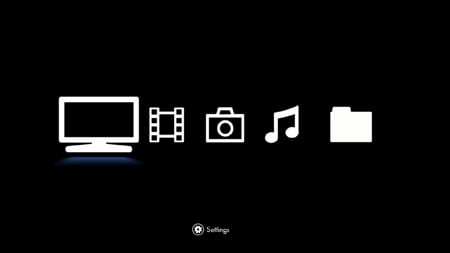
Basic icons identify the unit's key functions
The device’s on-screen browser interface is also quite straightforward. It displays a set of large icons, which represent the TV tuner, music, photos and video files that you can play on your TV, and it’s a simple matter to select the option you want by using the control pad on the small remote control.
When you select the TV icon, the Black MAX simply acts like a conventional Freeview recorder. Unfortunately, it’s not a terribly sophisticated Freeview recorder. It includes basic features, such as an electronic programme guide (EPG), and the ability to pause live TV.
However, other features are crudely implemented. The remote control doesn’t have a number pad, so you can’t quickly punch in a channel number to select a specific channel. You either have to scroll through the full on-screen list of programmes or go through a rather long-winded process for creating your own list of favourite channels.
Most digital recorders also include some sort of ‘series record’ option within their EPG for automatically recording all the episodes of a particular show, but the Black MAX requires you to manually schedule recordings by specifying the date, time and duration of the programmes to be recorded.

Screen idle: navigation latency is an unwelcome test of patience
The Black MAX’s menu system is also rather sluggish – we’d often find ourselves thumping buttons impatiently while waiting for various menu choices to appear on screen, and the option to manually programme a recording takes a good ten seconds to appear.
