This article is more than 1 year old
Malware house offered bounty for infected Macs
Fake OS X codec scam exposed
A researcher has unearthed fresh evidence of cyber criminals' growing attraction to Apple's OS X platform with the discovery of a now-disbanded group that offered 43 cents for every infected Mac.
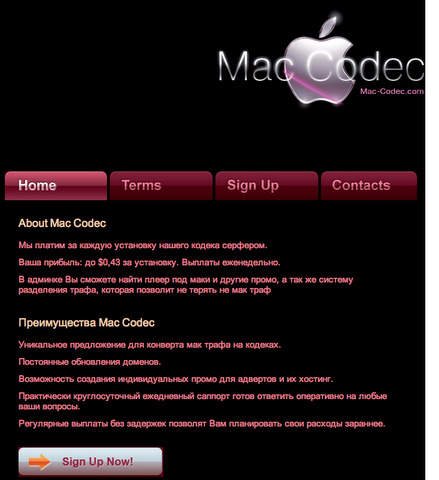
Mac-codec.com was just one of hundreds of "codec-partnerka," a term researcher Dmitry Samosseiko uses to describe the well-organized affiliate networks that pay a small bounty each time their malware is installed on an unsuspecting end user's computer. What makes this one stand apart is its dedication to the Mac platform.
"It's very infrequent," Samosseiko told The Register, referring to the finding he made earlier this year. "We discover new ones extremely rarely compared to Windows platforms."
The site advertised various promotional materials Mac-based "video players" and offered "webmasters" the fee in exchange for each installation on Macs that visited their exploit sites. The 43-cent fee is slightly lower than the 50 cents to 55 cents the codec-partnerka pay for infections of Windows-based machines, Samosseiko said.
The outfit was holding out the offer in January and February of this year, but has since closed its doors, said Samosseiko, who is manager of Sophoslabs in Canada, a research arm of anti-virus firm Sophos. He presented his findings as part of a larger discussion about codec-partnerka presented at this week's Virus Bulletin conference in Geneva. The groups' malware typically masquerades as legitimate video codecs or anti-virus software.
"I suspect that it wasn't as profitable to target the Mac platform at that point," he explained. Mac-codec.com "probably closed because it wasn't commercially viable for them to conduct business."
Infiltrating the highly secretive networks is by no means an easy task. Most of them are based in Russia or elsewhere in Eastern Europe, and interlopers must first gain the trust of other members. Although Mac-codec.com is no longer active, Samosseiko doesn't believe that's the end of the bounty program for infected OS X systems.
"I suspect there are others targeting other Mac users," he said. ®
