This article is more than 1 year old
Rock Xtreme X790
Desktop Core i7 in a notebook
Review The mobile version of Intel’s Core i7 processor isn’t due to arrive until early next year, so we were a little surprised to hear that UK system builder Rock was about to launch a new range of laptops based around the i7.

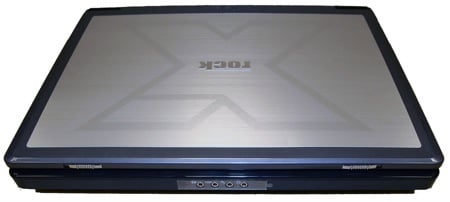
Rock's Xtreme X790-i7-950: built for speed, not for looks
A quick call to Rock confirmed that the company is using a standard desktop i7 processor. Our first thought was that this was an unabashed pitch for the gaming laptop market, but the Xtreme 790, Rock informed us, is simply intended to be “a very powerful all-round workstation”.
It also dropped hints about the police e-crimes unit using machines such as this to analyse server data, “though we can’t go into too much detail on that”, the company added enigmatically.
There are three models in the range, starting at £1999 with a machine featuring an i7 running at 2.66GHz. We tested the mid-range X790-i7-950, which runs at 3.06GHz and costs £2399. There’s also a 3.33GHz model that's priced at an eye-watering £2999.
To be honest, the X790 is nothing special to look at. Most laptops in this price bracket are pimped out with all sorts of go-faster stripes and gratuitous flashing lights in order to tempt the testosterone-charged gaming brigade. But, befitting its status as a workhorse, the X790 is clad in a sedate silver-grey with black trim.
Pitched as a workhorse rather than as a games machine
The glossy 17in screen has a native 1920 x 1200 resolution, and produces a bright and attractive picture, but there’s no option to choose the matte finish still preferred by many designers and photographers. It's driven by an Nvidia GeForce GTX 280M graphics processor with 1GB of dedicated video memory
