This article is more than 1 year old
Mac OS X Snow Leopard First Look
Our initial impressions of Apple's new baby
Installation and Upgrading
I installed Snow Leopard on a three-year-old quad-core Xeon Woodcrest Mac Pro, and a 15-month-old basic MacBook. Not exactly the latest and greatest hardware, but in both cases EFI reported a 64-bit system.
On the MacBook, I nominated to keep the Leopard partition intact, and reformat a Boot Camp Windows partition for Snow Leopard. I was a bit surprised to find I couldn't format this from inside the Installer - I needed to quit the Installer and run Disk Utility manually. But otherwise it was plain sailing. On the Mac Pro, I performed an in-place upgrade.
What greeted me was familiar: Snow Leopard starts like Leopard, down to the pixel.
Apple promises that Snow Leopard frees about 7GB from a comparable Leopard installation. This left me a bit puzzled. With X11 unchecked, but with the foreign language fonts installed, a clean install took up a shade over 10GB. Apple's system requirement is 5GB of free space.
Nevertheless, there's some serious shrinkage going on. Safari's public beta on Leopard weighs in at 45MB, but the Snow Leopard Safari at just 14MB. The Address Book shrinks from 58MB to 15MB. Mail is now 77.5MB.
The Leopard option to 'Open in Rosetta' is still there for PowerPC applications, but there's now an option to open 64-bit apps in 32-bit mode. I noted that for Safari, this was turned off, but Address Book started in 64-bit mode.
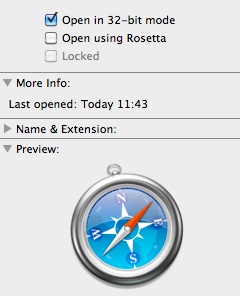
Safari starts in 32-bit by default
I discovered that Rosetta isn't a default installation option - you must customise the installation to include it.
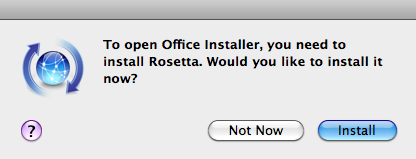
If you need Rosetta, remember to choose it at install time, or else you'll need your DVD.
Perhaps it's a licensing issue? Rosetta is the miraculous run-time technology developed at Manchester University by a computer science professor, who went on to found Transitive - a brief history here. IBM acquired the company last year. Rosetta smoothed the migration to Intel hardware enormously, and will be needed for some time.
It has been claimed that Snow Leopard will download Rosetta if it wasn't installed but you need it subsequently. We couldn't confirm this.