This article is more than 1 year old
Baby-roasting BBQ pulled from Sears site
Red-faced retailer apologizes
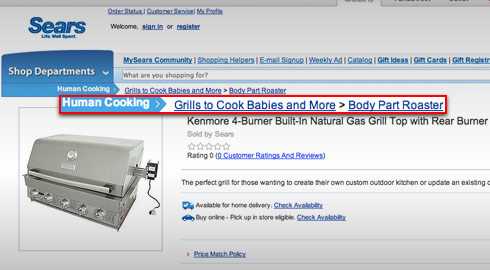
In a blunder that might top the Baby Shaker app on Apple's App Store, retailing giant Sears.com has been caught offering a Bar-B-Que grill specially designed to roast infants and other human morsels.
The ad, which was spotted earlier by celebrity news site TMZ, showed a Kenmore natural-gas grill with five burners. A caption above the photo read: "Human cooking > Grills to cook babies and more > Body part roaster."
Sears quickly labeled the cannibal-themed grill a prank that was carried out by someone visiting the company's website.
"We discovered earlier today that someone visiting our site had defaced a limited number of product pages," the company said in a written statement to FOXNews.com. "We've already taken steps to prevent this from happening again."
The company apologized for the incident and said there was no reason to believe customer data was intercepted during the security lapse.
The incident is the latest reminder that website security, as tedious as some corporate types may find it, does matter. Defacements like these are easy to prevent, but many companies don't bother to take action until it's too late. ®
