This article is more than 1 year old
What’s the point of desktop virtualization?
And what are the practicalities?
Reader Workshop Over the past few weeks we have considered many facets of virtualization and now we take a look at an area that has the potential to subtly alter the way in which the majority of users interact with IT services, namely the desktop. Research carried out by Freeform Dynamics last year with the help of readers of The Register showed that considerably fewer than 10 per cent of organisations had deployed desktop virtualization for live systems.
A quick scan at the chart below shows that the IT professional community was not overburdened with understanding in this area at that time.
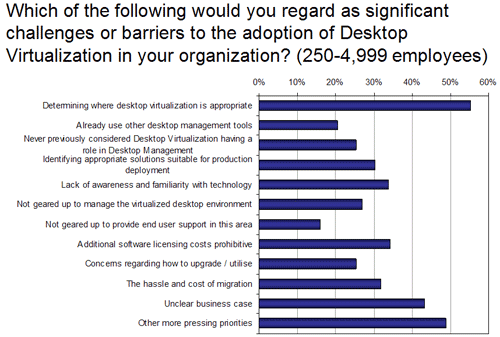
In particular, the business case for desktop virtualization was not terribly well understood, with less than one organisation in three having a clear rationale for the adoption. Even this was probably an overestimate as the sample was self-selecting and therefore almost certainly biased towards those more familiar with the topic.
Nevertheless, among those who responded, when it comes to challenges or barriers to the adoption of desktop virtualization, the small matter of "determining where desktop virtualization is appropriate" was ranked as the biggest issue, closely followed by "unclear business case" and "other more pressing priorities". A self confessed "lack of familiarity with the technology" highlighted that all parties had major work to undertake before starting major desktop virtualization projects.
Wind the clock forward, and it would be interesting to know if things have moved on at all over the past 18 months. Today's more prevalent desktop virtualization approaches (in which the virtual desktops themselves are run on servers, with their display's served up to desktop clients) are often considered under the banner of Virtual Desktop Infrastructure (VDI). If you have any thoughts on such approaches, particularly if you have started to investigate, pilot or roll out VDI solutions, we'd love to hear some of your experiences in the comment section below.
In terms of practicalities, our own view is that the rational place to start is to consider just what desktop systems are currently deployed and what desktop services are being used by whom. At heart this amounts to having an up to date desktop asset repository which can be used as a foundation for objective analysis. After getting such information and working out what solutions fit where, it is worthwhile remembering that any desktop virtualization implementation does not have to be an "all or nothing" undertaking. Instead, mixing the many offerings available may be the most appropriate fit to a range of business needs.
If you have any thoughts on this, again we would like to hear from you, e.g. your experiences with regard to use segmentation, targeting of deployments, and so on.
Looking at a specific set of use cases, one of the areas that some VDI solution suppliers have been keen to promote, is the provision of access to corporate systems from private PCs. Similarly, some feel that providing contractors and other outside parties access to select corporate systems would be another hot area for VDI deployment. In the US a number of organisations have begun to experiment with variations on this theme: instead of supplying users with corporate PCs they provide them with an allowance with which they can purchase a machine of their choice. This machine then has a desktop virtualization system laid upon it and corporate access is delivered in an isolated virtual machine on the desktop thus in theory completely separating corporate and personal use.
We have yet to see if this takes off outside North America, and any opinions from readers in Europe or other parts of the world would be interesting to hear on this topic.
If there are other aspects of desktop virtualization you would like to comment on, please go ahead. Are you, for example, happy that you have a good idea of what is available from the traditional Thin Client / Terminal Services / Citrix type offering through to the newer virtual desktop and application streaming options? Have any tips or workarounds for some of the challenges that came out of our research? Are skills and experience available, either internally or from outside the business? How easy are they to come by and keep?
Please feel free to join the debate by adding your comments below.
