This article is more than 1 year old
D-Link Xtreme N DIR-685
Another stab at router convergence
Imagine your next-door neighbour mowing the lawn, and that’s the kind of tone you get from it. A tiny fan pointing out the top right of the device, which spins whenever the hard drive is in use, is the culprit. The DIR-685 is silent when the hard drive winds down, but start transferring files and it will drown out a modern desktop PC.
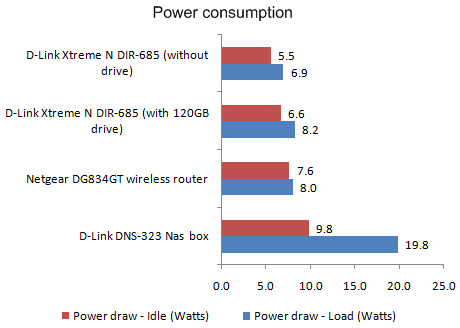
Power consumption is excellent, especially compared with discrete devices
What this device is crying out for is a metal heat-dissipating chassis and a bigger and a slower rotating fan to reduce noise. Scheduled hibernation is also lacking and would be especially useful if you sleep near the router, so you’re not awoken in the middle of the night thinking your neighbour is trimming hedges.
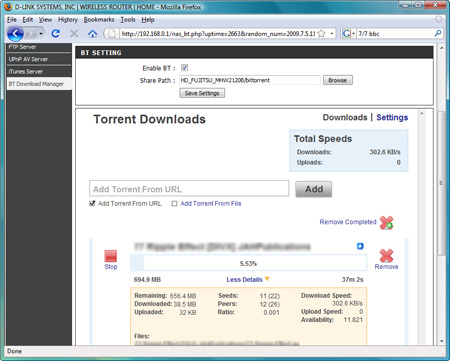
The web interface resembles many other D-Link router layouts. The main difference is the Storage tab that lets you enable Nas features like the FTP server, UPnP server and iTunes Server. Bittorrent files are downloaded in via the web interface too and immediately made available for sharing over UPnP, if you have it enabled.
It passed our DLNA test by streaming a 1080p movie to a Playstation 3 – although it didn’t have enough grunt to fast forward through the movie effectively – and it was also fine streaming films to an Xbox 360.
To simply access the DIR-685’s USB ports took about a day. The necessary steps to configure them just aren’t provided. While any other Nas unit would have this facility working out of the box, with this device you have to instal a utility called Shareport. However, we couldn’t get this software working at first because you have to run the setup utility on the CD first. Instead, we just installed the latest version of Shareport from D-Link’s website, which wasn’t good enough to get it going. Run the CD setup, then get the Sharepoint download installed and you’re in business.
Even so, USB drives and printers can only be accessed by one user at a time and Linux users can’t access USB devices at all, which is a frustrating limitation other Nas boxes don’t have. Furthermore, the Nas functions don’t support Apple’s Time Machine or provide any backup scheduling software. You just get the impression that this is an incomplete package, in more ways than one.