This article is more than 1 year old
Kingston SSD Now V
Excellent bang for your solid-state buck?
Review Kingston Technology offers three distinct families of SSD, with the SSD Now E series for servers and the SSD Now M series aimed at mainstream performance PCs. These models are exactly the same as the Intel X25-E and X25-M drives, no doubt thanks to the IM Flash Technologies joint venture between Intel and Micron.

Kingston's SSD Now V: does the 'V' really mean 'value'?
The third series of Kingston drives is SSD Now V - 'V' for 'value' - which is a solo effort by Kingston. Intel played no part in the development of these drives.
The hardware inside the SSD Now V comes as something of a surprise as the chips are all made by Toshiba. On one side of the board there are eight TH58NVG6D 1D TG20 Flash chips and on the other side there are eight more of these and a TC58NCF602GAT controller chip. We’re not familiar with Toshiba Flash controller chips, but Kingston tells us that the 602 in the middle of the model code is significant as it indicates the chip is a JMicron 602 that has been fabbed by Toshiba.
That’s right, the JMicron 602 that is legendarily famous for stuttering when you transfer small files, open web pages or send an email. We can't be sure exactly which version of the JMF602 is used in the SSD Now V as there has been at least one revision to the chip, but we are clear that manufacturer OCZ put two JMF602 chips together in Raid mode to create the Apex SSD to avoid those sorts of problems.
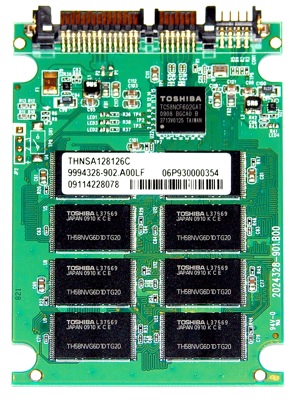
The Toshiba chip out on its own is really a JMicron controller
We tested the SSD Now V in combination with an Intel X25-M and a Patriot Torqx. Patriot uses an Indilinx controller, while Intel uses its own. We also ran the Kingston SSD alongside a 7200rpm 1TB Western Digital Caviar Black desktop HDD and a 5400rpm 500GB Toshiba HM500LI laptop hard drive.
