This article is more than 1 year old
Cutting the cord: future mobile broadband tech
How internet on the go is going to get much faster
The original wireless data was based on CSD (Circuit Switched Data) connections: using the connection that would normally carry a voice to transport data. The problem with CSD, apart from its lamentable lack of speed, is that the amount of bandwidth used remains the same even if no data is being transmitted. Early Wap sessions were commonly billed by the minute like phone calls.
From 2001, the 8390: Nokia's first GPRS phone
That changed with GPRS (General Packet Radio Service), which did at least use a digital connection and one that slipped packets into unused voice slots rather than converting data into audible tones. But the speed was still poor and mobile data only expanded from the specialist to the geek - still far from the mobile internet promised in the adverts.
The slots available to GPRS exist because while GSM is an FDD (Frequency Division Duplex) technology it's also TDMA (Time Division Multiple Access). The first term means that one frequency is used for sending and another, simultaneously, for receiving. That's in contrast, incidentally, to TDD (Time Division Duplex) where the same frequency flips between send and receive many times a second.
TDMA means that where more than one user is on the same frequency they are allocated time slots in rotation, up to eight of them in GSM, later upgraded to 16. If fewer than eight people are on the same frequency then GPRS can drop data into those unused time slots.
Handsets have even got quite good at using more several slots. Up to four are commonly used giving a speed something in the region of 53.6Kb/s with a following wind, if the empty slots are available - voice still takes precedence every time. That's a huge improvement, but users still proved obstinately slow to embrace mobile data.
3GPP GSM/GPRS/Edge Timeline
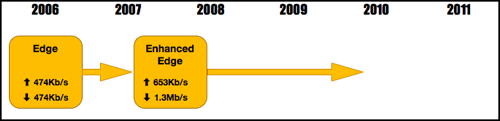
Then we were told that Edge (Enhanced Data rates for GSM Evolution) would deliver what we had been promised. Edge uses better encoding than GPRS to squeeze three times the data into the same slot, usually with a basestation and handset software upgrade as everything but the data encoding remains the same.
