This article is more than 1 year old
Vulture Central unleashes RegPad™
Redefining the web-surf Linux tablet paradigm
Finally, let's have a look at some possible paradigm-busting practical applications of the RegPad™:
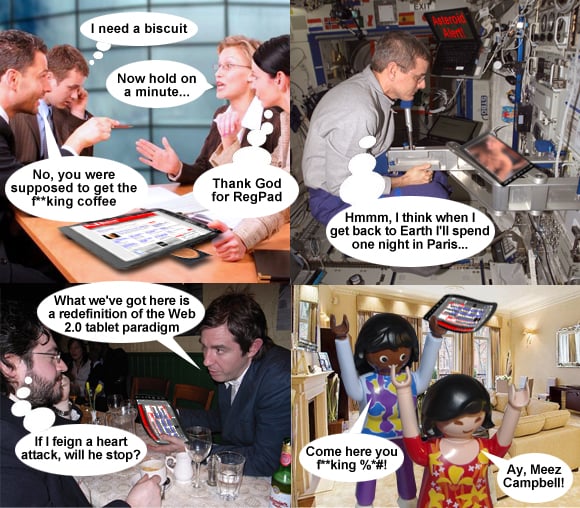
First up (top left) we see RegPad™ as the the ultimate solution to the corporate power brunch brainstorm coffee catastrophe scenario. Mercifully, at the touch of a button, a quick-thinking adsales girl has commanded the RegPad™ to requisition caffeine, and plenty of it.
On the International Space Station, meanwhile, the RegPad's Delay Tolerant Networking capability allows bored astronauts to acquire quality smut vids from a bittorrent server hidden on Martian moon Phobos. Whereas a lo-res jpeg of a Natalie Portman nipslip previously required around a week of downloading, space surfers can now enjoy HD-quality grumble flicks streamed in pretty well real time.
At bottom left, we see the advantages of the virtually-indestructible RegPad Flex™ during recent field testing by Phillipe of Vulture Central's Strategy Boutique in our local boozer.
The Flex proved immune to beer and vigorous waving in the air, as demonstrated here. Its scratch-resistant screen also provided a handy surface for the preparation of Bolivian marching powder, which eager volunteers hoovered up their nostrils while being served pop-up ads for related online pharmaceutical offers, courtesy of The Register's behavioural-tracking software, acquired from Phorm.
And finally, the RegPad Flex™ looks set to become the weapon of choice for battling supermodels, the better to beat their terrified lackeys without the kind of fear of terminal damage which always makes BlackBerry-based assault a less fulfilling experience.
The RegPad™ and RegPad Flex™ are set for launch later this year, prices TBC. Biscuits are not included. Using a RegPad™ to thrash your personal assistant may void the warranty. If in doubt, consult your legal advisor. ®
