This article is more than 1 year old
The best memory config for a Core i7 CPU
All the options tested
When Intel launched Core i7, the integration of the memory controller in the CPU core marked a major change from the Core 2 architecture. Intel was relatively slow off the mark in this regard: AMD moved the memory controller from the chipset to the CPU die in 2003 when it launched the Opteron.
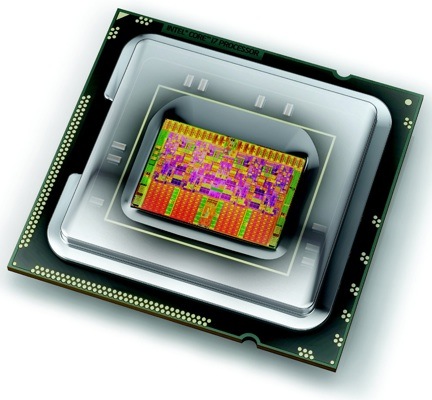
Intel's Core i7: the first Core with an on-board memory controller
Since then we've seen a dual-channel 1066MHz DDR 2 memory controller in AMD’s Opteron, Athlon 64 and Phenom processors, and this has been updated in the latest models of Phenom II and Opteron with the addition of a dual-channel 1333MHz DDR 3 controller.
Intel took a different approach with Core i7 and used a triple-channel DDR 3 controller to increase the memory bandwidth without requiring high memory clock speeds.
The chip giant stipulated a surprisingly low default memory voltage of 1.5V. Although the Jedec standard for DDR 3 includes an operating voltage of 1.5V, it's common to find that a higher voltage of 1.7V or 1.8V is necessary for the sort of clock speeds that we're used to seeing with Core 2 and Phenom II.
Motherboard manufacturers felt it was necessary to warn customers that raising the memory voltage above 1.65V could damage a Core i7 processor, although we see that they continue to offer overclocking options that would take the memory way beyond 2.4V.

It took a few months for low-voltage Core i7 DDR 3 memory to start rolling in from the manufacturers and naturally those kits contain three modules of memory rather than the traditional pack of two.
