This article is more than 1 year old
Asus Crosshair III Formula AM3
Top-notch gaming performance
The two power connectors are positioned at the edges of the board, the two PCI Express 2.0 x16 graphics slots are widely spaced, and the ATA-133 and Sata connectors are laid down for easy cable connection. Pedants will note that four Sata connectors are laid down and one stands vertically. Regular folk may wonder about the odd total of five internal Sata connectors. The SB750 southbridge chips supports six Sata connections, and as Asus has specified an eSATA port on the I/O panel, that leaves five available inside.
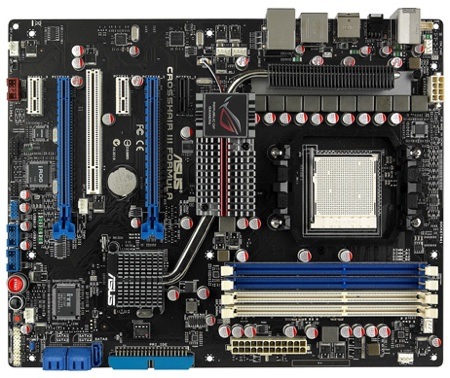
Top down: another view of the board
The Republic of Gamers features include a SupremeFX X-Fi audio card that plugs into the top-most PCI Express x1 slot leaving two PCI Express x1 slots free for further expansion. The SupremeFX card carries six audio mini jacks along with coaxial and optical S/PDIF outputs which leaves the I/O panel looking incredibly bare as it only carries one PS/2 port, six USB ports, a single Firewire, one eSATA and Gigabit Ethernet.

A SupremeFX X-Fi audio card is included
The package includes a bracket that carries two more USB ports and a second Firewire port, and there are headers for four more USB ports on board - handy if you have case-mounted ports.
There are Republic of Gamers extras in the shape of an external Reset button on the I/O panel, while at the foot of the board you get Power, Reset and Clear CMOS micro buttons. Asus also includes its External LCD Poster, which is a small LCD gizmo that plugs into a connection just behind the I/O panel.

The Poster translates Post error codes into English
The cable feeds out through the I/O shield and is long enough to allow you to position the LCD Poster on top of the tower. In the event that a problem occurs during Post, the LCD Poster will deliver an error report in proper English instead of the usual indecipherable hex code.
