This article is more than 1 year old
O2 Joggler family organiser
More PMP than parental PDA
Audio quality was also better than we expected from a device with no EQ, bass, treble or sound modification settings. We loaded up a selection of music and plugged in our reference Sennheiser HD-25s. Playback delivered a well-focused and balanced sound, solid bass and good stereo separation, with plenty of volume on tap too.
Tinny speakers, but audio sounds good through headphones
If the Joggler has a failing as a media player, it’s the lack of anything in the way of a progress bar or FF/REW button which makes skipping to a specific part of an audio or video file impossible. The absence of ID3 tag support may irritate some users too.
As a digital picture frame the Joggler is difficult to fault. Just slot in a USB stick full of images, set the image duration time and press play. It’s as simple as that, with the displayed images being both colourful and sharp.
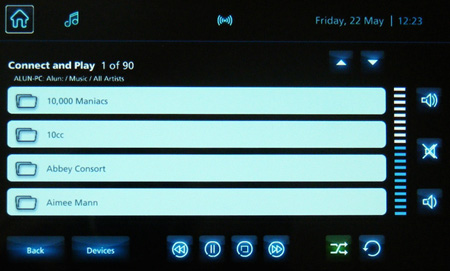
The Joggler has only 1GB of internal storage, but that's not quite the drawback it could be. To start with, you can use the USB interface to play media from a memory stick but, being also UPnP compatible, you can also stream media from a computer hard drive or Nas.
In our view the Joggler's ability to work as a stand alone wireless media streamer rather overshadows its calendar functionality. Hook the Joggler up to a cheap and cheerful Nas box like the EZY Technologies MyXerver we looked at recently and you have 24/7 access to your media from your bedside or kitchen table.

The timely standby screen
Streaming aside, the process of filling that 1GB of storage has been tailored so that even the most PC-phobic should be able to manage. Simply plug in a USB stick, touch the 'USB' button when it lights up then tap the check boxes next to the files you to wish to add to the Joggler then tap 'next'. Not allowing users to add and remove content via Windows Explorer does strike us as taking the whole ‘simple to use’ ethos just a bit too far though.
