This article is more than 1 year old
Remembering the true* first portable computer
*The one that melts your face off
A big hit (metaphorically)
After a successful initial test flight in 1961, the US Department of Defense formally green lighted the Minuteman program. The missiles turned out to be a big hit, although thankfully never literally.
But it's important to note the system represents more than Cold War posturing. The computers we use today owe quite a deal to the Minuteman program.
Advances in technology combined with president John F. Kennedy's switch to a "flexible response" regime to a potential Soviet strike drove home the need for a new generation of Minuteman missiles. A new requirement of being able to re-target and reprogram a missile moments before launch was something the Minuteman I's discrete circuitry simply wasn't up to. Because of that, Autonetics turned to integrated circuits for the Minuteman II's navigational computer. This change in tech nurtured IC production in its infancy through the early 1960s from pioneering companies like Westinghouse, Texas Instruments, and RCA.
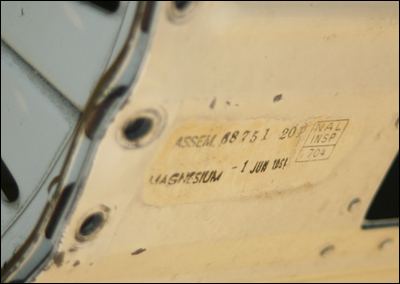
Minuteman II's navigation system was nearly one quarter the size of Minuteman I with approximately two and a half times as much memory. Midway through the decade, the Minuteman project was responsible for about 20 per cent of all IC sales and had become the largest purchaser of semiconductor microcircuits. While the American government's direct contribution of integrated circuit R&D is arguably modest, it was undeniably the technology's sugar-daddy.
We should celebrate this wonderful nuke. Oh sure, the computer system couldn't run "Wordstar" or a game of "Colossal Cave," like the Osborne 1, but how many computers do you know that can destroy the world? That feature offers some serious LAN-party cred right right there. And with a three-stage, solid-propellant rocket build in, travel is a breeze.
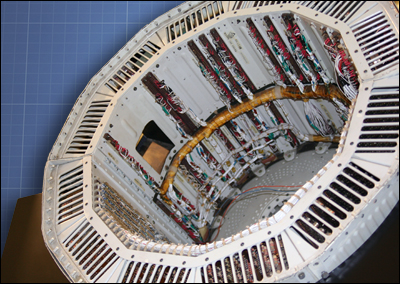
As always, our thanks to the Computer History Museum in Mountain View, California for letting us drool over their machinery. For those interested in finding more Minuteman 1 history and data, check here and here for a megaton. ®
