This article is more than 1 year old
Dutch cat skinner publishes critics' personal details
Kitty handbag artist tracks hatemailers across cyberspace
The Dutch "artist" who in 2004 turned her pussy into a handbag under the performance art title "My dearest cat Pinkeltje (2004)" has published personal details of those who emailed her expressing their disgust.
 Katinka Simonse, aka Tinkebell, copped a veritable shitstorm of e-abuse for the feline fashion accessory stunt (pictured), and she and fellow artist Coralie Vogelaar decided to track down the senders, sniff out their intimate online secrets and present the whole thing for public consumption.
Katinka Simonse, aka Tinkebell, copped a veritable shitstorm of e-abuse for the feline fashion accessory stunt (pictured), and she and fellow artist Coralie Vogelaar decided to track down the senders, sniff out their intimate online secrets and present the whole thing for public consumption.
The result of trawling the net in search of their prey is the pair's Dearest Tinkebell, which includes the contribution of a 19-year-old American woman who wrote: “HAVE A GREAT DAY YOU GROSS DEAD CUNT."
For her trouble, the missive's author is now named and shamed, complete with photographs, the name of the town where she lives and her Amazon.com wish list. This includes "a pedal exerciser" and a "Ladies Cotton Rubber Posture and Tummy Control Fat Burner".
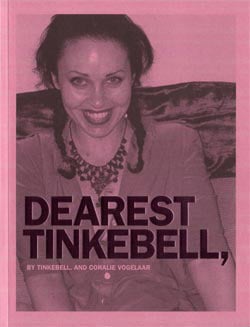 According to Tinkebell's Facebook presence, the book (see pic) is intended to confront "head on" the "apparent anonymous practice of online threatening of public or semi-public individuals" and "evaluate hatemail as both a social and artistic phenomenon".
According to Tinkebell's Facebook presence, the book (see pic) is intended to confront "head on" the "apparent anonymous practice of online threatening of public or semi-public individuals" and "evaluate hatemail as both a social and artistic phenomenon".
Vogelaar said: “It was shocking to see how much personal information you can simply find on the internet. Strikingly, these people who send threats are often quite exhibitionistic, and they have published hundreds of photos of themselves on the internet. They want to show it all, and think that everybody is interested in everything they do.”
Nieuws Uit Amsterdam notes that the authors are aware "they may be violating privacy or copyright law" and that legal action could follow. Tinkebell insisted that anyone attempting litigation would be reported to the police for the original abuse.
The first rumbling of discontent at Dearest Tinkebell came from a "48-year-old communications consultant and wife of a controversial plastic surgeon from Amsterdam" who told a local TV station she wasn't best impressed with having her details published.
She apparently objected to the artist's catbag with the email: “Girl, You don’t often see a freak as disturbed as you are. You think you can do this to the animals. I’m going to personally make sure that you’ll stop what you’re doing. You’ll regret this.” ®
Tinkebell's other illuminating works include a "radio-controlled hamster and musical-box cat", which she says are "bound to raise a few eyebrows". ®
