This article is more than 1 year old
'Thieving' sperm whale caught on CCTV
Cetacean crime wave hits Alaska
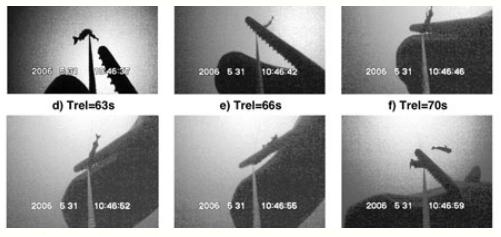
Boffins working with Alaskan fishermen have used CCTV to capture unique video of a sperm whale attempting to scoff cod off fishing gear. Such behaviour is referred to as "thieving" by the fishermen.
Do you know this whale?
The vid, which can be viewed by clicking here, shows a longline deployed at a depth of 100m off Sitka on the coast of Alaska. Fishermen in the region have found that crafty sperm whales, operating uncharacteristically in gangs, will often nab the cod off their lines. They see this as stealing, though of course the whales might have a different take on the situation.
In any case, seeking a way to stymie their cetacean rivals, the local fishermen teamed up with boffins from the Scripps Institution of Oceanography in California - even going so far as to attach CCTV to their fishing equipment, just as one might when faced with land based burglars.
The Scripps boffins were actually more interested in finding out about the sound signalling used by the whales: thus far, scientists have been able to pick up a lot of sound records but never with any clear idea of the size of the whales emitting them.
"The sounds can be louder than a firecracker," says Aaron Thode, a Scripps researcher. "Until this video recording was made, scientists had not been able to get a measurement of the size of the animal's head and the foraging sounds at the same time."
It seems that Thode and his colleagues may be able to use their results to carry out censuses of whales in an area merely from their acoustic signals, or even learn to recognise and track individual whales across the oceans.
"That's something people have been fascinated by for a long time," says Thode. "Humans can recognize individual people over the telephone using features of their sounds, but it's been quantitatively very difficult to do this for individual animals."
Meanwhile, it seems that the crimebusting CCTV vid has also unmasked the modus operandi of the cetacean cod blaggers. According to the Scripps Institute, the crafty mammals "pluck the line at one end to jar the black cod free at the other end, somewhat like shaking apples from a tree".
The boffins reckon this info will help the fishermen preserve their catches, though they don't say how. Read all about it from the Scripps Institute here. ®
