This article is more than 1 year old
Wolfram Alpha - a new kind of Fail
Welcome to the internet, Stephen
Comment Wolfram Alpha, the not-quite-search-engine from self appointed mathematical genius Stephen Wolfram, launched last Friday, and oh my, has it been a great weekend for software reviewers. I took some time to play around with Wolfram Alpha, and aside from being the best damn Wikipedia search engine since Powerset, the only noteworthy thing about it is that so far, Alpha is the finest example of the tragedy that results when an academic tries his hand at building a successful web product.
I know that in evaluating a Stephen Wolfram production, my meager intelligence quotient may not be sufficient to grasp the gravity of what I'm dealing with. So I don't feel all that put down that I can't figure out how Alpha is useful to anyone outside of a small audience of college professors and professional engineers.
Alpha is really good at telling you all sorts of information about mathematical expressions, showing you publicly available data about populations and geography, and comparing stock quotes. However, I am a software engineer by trade, and the information I need is about Python module documentation, Apache configuration, and why some fucking snippet of CSS won't fucking render in fucking Internet Explorer fucking 6. For someone like me (and in the web market, there are a lot of people like me), Alpha is breaking ground in a New Kind of Uselessness.
Maybe I'm being too hard on Wolfram. After all, when industrial recruiters want to hire people, they don't cruise the local science fairs, but a blue ribbon for your three-panel magic marker and pipe cleaners display on natural language processing and artificial intelligence really sets you apart from all of the other nerds. So, let's see how Alpha does on a relative scale. I have some experience in building a search-related web product, so I can tell you for sure how most users' first interactions with a new search engine go.
Step 1: search for your own name.
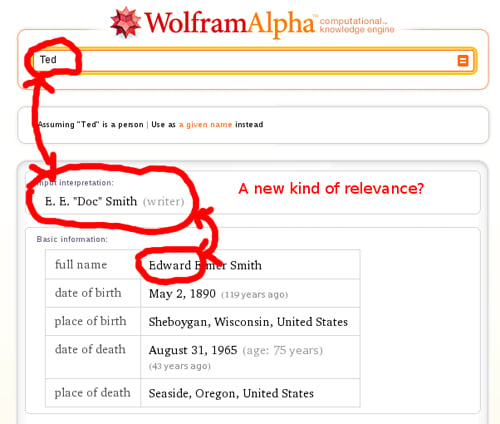
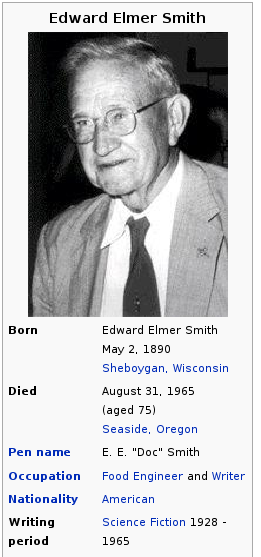
So this fellow is the Ted? Impressive. The real sticking point here is that this data is lifted directly from Wikipedia. This is the sidebar of the Wikipedia page for Edward Elmer Smith:
While Alpha doesn't directly credit Wikipedia with this information, it does provide a link as "related." The primary "source information" for this page is "Wolfram|Alpha curated data, 2009." The Wikimedia foundation is listed as a "background source or reference." I guess that's a New Kind of Plagiarism.
