This article is more than 1 year old
Gadget charger harnesses sunlight and wind power
Hydro-electricity not supported... yet
Much has been written about solar-powered gadgets and chargers, but what if there isn’t much sunlight around when your iPod runs flat? Well, according to one manufacturer, a little wind’s all you need.
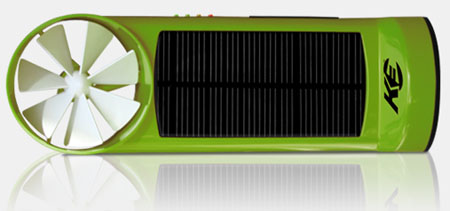
The K3 generates power from sunlight and from wind
Kinesis Industries’ K3 is a gadget charger able to collect juice from sunlight, wind power or a combination of both.
The 78 x 236 x 8mm handheld unit has a rechargeable lithium ion battery inside that, after one hour’s worth of sun soaking and wind whirring, can generate enough power to provide, on average, 30 minutes of mobile phone talk time.
Alternatively, the same length of eco-friendly charging time can generate 300 minutes of MP3 music playback.
A series of LEDs down one side show you how much power’s been soaked up so far and the gadget even has a small hollow section where you can keep your various power adaptors, such as USB and Micro USB cables.

A hidden compartment holds power adaptors
But if the sun stops shining and the wind stop blowing, then K3 also works just as well as a mains-sourced portable power unit thanks to the bundled AC power adaptor.
The K3 will blow in this June, but a price hasn’t been mentioned yet. ®
