This article is more than 1 year old
The Netbook Newbie's Guide to Linux
Back to the Bluez
Episode 5 I opened up my Acer Aspire One again after a prolonged interval while I was involved in a very different project and was puzzled to discover that Live Update was offering me a "Bluetooth patch". It's not just that the hardware doesn't have Bluetooth - that's easily fixed by plugging in a dongle - but even if you do plug in a dongle, the operating system remains blissfully ignorant of it. I assumed this was because there's no Bluetooth support in the kernel supplied with the AA1's version of Linpus.
I decided to install the update anyway - with some reservations: see Is it Evil. The standard Linux Bluetooth software suite is Bluez, and presumably the Acer offering was based on this, so with hope rising in my heart I plugged in my subminiature Bluetooth dongle. You can pick these little fellers up in Maplins for around £20, but my preference was for an eBay purchase, which cost me all of £3.40 - including delivery!
When these things are conferring happily with the operating system a tiny blue light flashes in the depth of their being. The light can be faint, and you might need to cup your hands over the device to see it, but it's there. I cupped and peered. Alas, there was no blue light. Damn.
This could mean one of two things: either I was right about there being no Bluetooth kernel support, or the device itself was for some reason inherently unrecognisable by Acer's Linpus - although I knew it worked OK with Windows. A simple command line utility solved that dilemma straight away: lsusb.
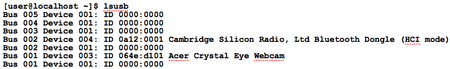
My lsusb output
...and there it is, the little darling. British, too. A device that the lsusb 'list USB' utility could find, but the kernel didn't know how to use.
Clearly, what was missing were the relevant kernel modules - but see What's Really Missing. I can understand why Acer might omit Bluetooth hardware, and therefore core Bluetooth software from the machine, but to issue a "Bluetooth patch" that adds the tools without the core kernel modules seems totally daft.
I queried Acer UK marketing about this, and I'm still waiting for them to get back to me.
Meanwhile, we can fix the problem ourselves, thanks to a generous contribution from a discussion group contributor called linker3000 in the Aspire One User Group.
