This article is more than 1 year old
Microsoft follows Google to Mars
Any pics you can post...
Microsoft clearly will go to the ends of the Earth to make sure no Google product goes unanswered.
Weeks after the ubiquitous search engine unveiled new up-to-date NASA imagery of our celestial neighbor on Google Mars, Microsoft is touting its own Red planet-snooping pact with the space agency.
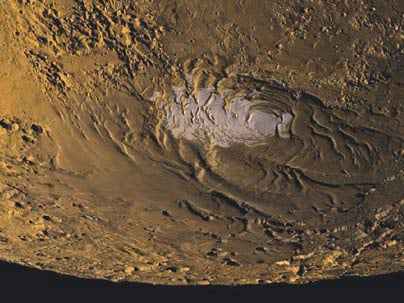
Under a joint agreement announced today, NASA's Ames Research Center in Mountain View will process and host more than 100TB worth of high-resolution scientific images and data from Mars and the moon which Microsoft will incorporate into its online virtual telescope, WorldWide Telescope. (Which itself was Microsoft's answer to Google Earth's Sky mode)
Microsoft to get your ass to Mars
The data set includes images taken by NASA's Mars Reconnaissance Orbiter, which launched in 2005. Later, they'll include images shot from the Lunar Reconnaissance Orbiter when the data is released publicly this May. While NASA provides much of the data online already — the agency's archive rather lacks the web 2.0 touch.
"This collaboration between Microsoft and NASA will enable people around the world to explore new images of the moon and Mars in a rich, interactive environment through the WorldWide Telescope," said Toney Hey, Microsoft's veep of external research. "WorldWide Telescope serves as a powerful tool for computer science researchers, educators and students to explore space and experience the excitement of computer science."
Meanwhile, NASA says it's happy to make the fruits of America's space program more accessible to the public.
The imagery will supplement existing pictures and data available on NASA's Planetary Data System website, which as we mentioned above, will scare the pants of anyone not certifiably a geek.
Microsoft's Worldwide Telescope is offered as both a Windows-only download and a web client (powered by Silverlight, naturally). ®
