This article is more than 1 year old
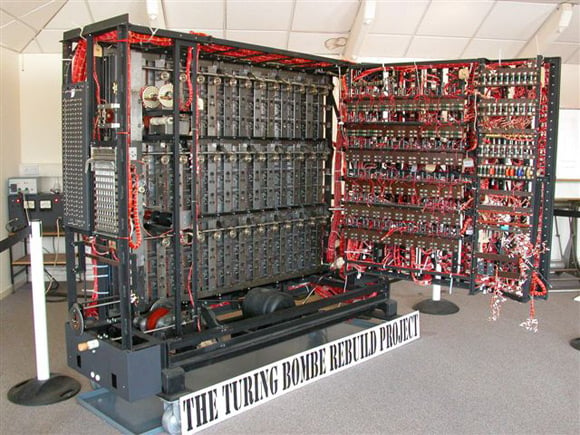
Bletchley Park fires up replica Turing Bombe
Engineering award for legendary Enigma-busting kit
Bletchley Park will tomorrow fire up a replica Turing Bombe to celebrate the Engineering Heritage Award which recognises the 13 years of hard graft which have gone into recreating the legendary Enigma-busting kit.
The Bombe was the brainchild of Alan Turing and Gordon Welchman, and the 210 machines manufactured by the British Tabulator Machine Company did vital work cracking encoded German military traffic - a feat which shortened the war by two years, Bletchley Park suggests.
The original devices were destroyed after the war on security grounds, but in 1970 a set of blueprints turned up at Bletchley and the idea to reconstruct a Bombe was born. The rebuild team, led by volunteer John Harper, has finally succeeded in putting the beast together:
Tomorrow's midday ceremony will reunite war veterans with the Bombe and feature a "live demonstration" of the machine. The Engineering Heritage Award* honouring the project is the 48th such trophy given by the Institution of Mechanical Engineers.
Bletchley Park Trust CEO, Simon Greenish, enthused (with some light tin-rattling): “The Bombe is just one of a number of incredible historic pieces we are proud to hold. Unfortunately, many of our iconic buildings at the park are now so dilapidated that within two years they could be lost.
"By raising awareness of projects like the Bombe we are highlighting how important the Park is and remembering just how indebted we are to the brilliant minds of the men and women who worked here. We are delighted that we can reunite some of those people with the Bombe.” ®
Bootnote
*Bletchley Park explains: "To win an award the object must be industrially innovative; be associated with a person or event, which has made a significant contribution to society and/or mechanical engineering, or possess a unique feature, by being a prototype or only surviving example."
