This article is more than 1 year old
TinyURL, your configs are showing
Twitter pal leaves server wide open
TinyURL - the site that converts unwieldy web addresses into short, manageable URLs - has been caught running a server so poorly configured it represents a serious risk to its millions of trusting users, a security expert is warning.
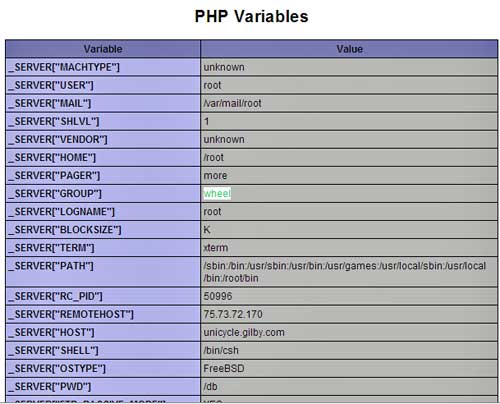
At time of writing, the site's PHP module was actively broadcasting dozens of sensitive configuration settings. The information, which includes the web server's IP address, operating system and web application server, are all included, making the job of penetrating the widely-used service that much easier.
Even more remarkable, the server user is listed as root, and its group is wheel. These so-called "god" settings would allow anyone who is successful in breaking into the box to maximize the damage that could be caused. Even novice server admins know they should run the server in a setting known as "nobody" or something similar, which protects sensitive parts of the server from tampering.
"This is the epitome of bad-practice," security consultant Rafal Los told The Register a few hours after publicly disclosing the misconfiguration on his blog. "Why would you want to run a web service as 'Administrator' because if I figure out a way to jack that service, I completely, 100% own that machine."
Los said he sent email to TinyURL addresses on Wednesday morning California time but never received a response. Emails The Register sent to various addresses, including one belonging to the site's founder, Kevin Gilbertson, weren't returned at time of writing. We'll be sure to update this story if we hear back.
The site's sloppy administration is much more than a mere curiosity. Because TinyURL significantly shortens long URLs, it's impossible it can be difficult for some end users to know where one of the site's links leads until they click on it. That makes the site the perfect vector for sending people to websites used in spam, malware attacks and other online scams. TinyURL's popularity has skyrocketed in the past year as it became the main way people on Twitter to share links.
The misconfiguration came to light through the collective sleuthing of Los and several readers of his blog. After noticing some strange errors in Twitter posts made by Fox News, Los originally suspected flaws in the online microblogging site. With the help of a user named Mubix and others, they quickly realized the errors were the result of poor practices at TinyURL. ®
Update
About four hours after this story was published, Gilbertson responded with the following statement: "That security 'expert' sure doesn't know how to read that. No daemons are run under an administrator or root user."
This story was corrected to reflect that it's not impossible to know where a TinyURL link leads. The site offers a preview feature.
