This article is more than 1 year old
Sony Ericsson Walkman W705 music phone
Add GPS and it becomes the W715
Sony Ericsson implements its familiar user interface, based on a main menu grid which can be switched to a rotating carousel or single, scrollable icon views. Sub-menus and functions are arranged logically. In some apps, the W705's motion sensor will auto-flip the screen orientation depending how the phone’s being held.

The Walkman app's as a good a music player as you'll find on a phone
The W705 has a camera key and zoom/volume rocker on the side. On top of the phone, a miniscule Walkman key provides a quick way into the music player. In tune-playing mode, it also works the motion-operated Shake Control: hold it down and shake the phone one way or another to fast-forward or rewind through tracks, adjust the volume or randomise the play order.
It’s a gimmick and it adds little practical functionality to the phone. Apart from shuffling, the other controls are at hand anyway. Pushing buttons is also more reliable, with less danger of sending your phone flying.
The Walkman player is still star of the show. It has an easy to operate, attractive user interface, supporting cover art when available and SensMe mood-generated track selection. SensMe works by tagging tracks in Sony Ericsson’s PC-based Media Manager software. On the phone, songs can be selected on a SensMe graph charting mood against tempo.
Sony Ericsson has also included a version of the BBC's iPlayer which can stream live and archived radio and TV programming straight to the handset over Wi-Fi, though 3G streaming isn’t supported. It's a breeze to operate and plays well, and is a nice accompaniment to the bundled YouTube app.
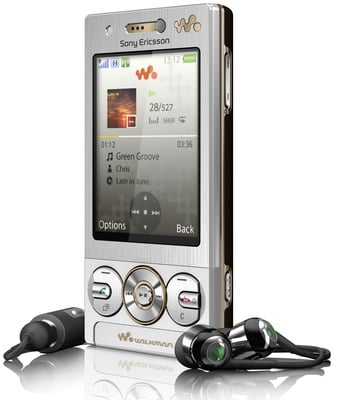
Comes with decent cans
The built-in RDS FM radio provides another serviceable source of entertainment. It can play through the loudspeaker even with the earphone cable connected as its antenna. Track ID software is part of the radio armoury as well as being usable for automatically identifying other tracks you hear around you.
