This article is more than 1 year old
How to upgrade an Acer Aspire One netbook's memory
Screwdriver at the ready
9. Starting with the rear right edge, slide your card or (gently) the flat-blade screwdriver into the casing between the lower black section and the upper blue or white plastic. Slowly move the tool forward and, as you do, you'll hear the case's clips pop open.
Do the two sides first and then the front, which is a little trickier to do - so take your time. Again, the credit card is the best choice of tool here, as it'll minimise scratching.

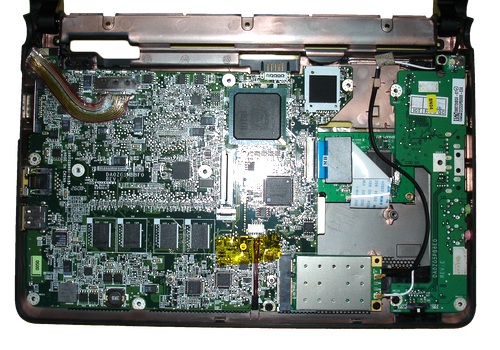
10. Lift off the lid to reveal the AA1's motherboard, wireless card and, to the right, daughterboard.
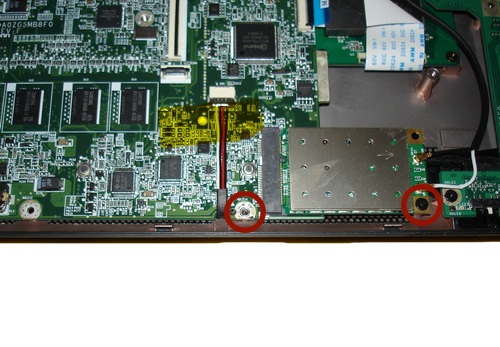
11. Remove the marked screws. The one on the right holds the wireless card in place - once free, the card will spring up and you can slide it out of its slot and move it to the rear of the case.
Take care with the screw on the left. It's in tight, and we nearly stripped the head getting it out. If you don't have a screwdriver that fits the screw's head, don't proceed until you have one that does.
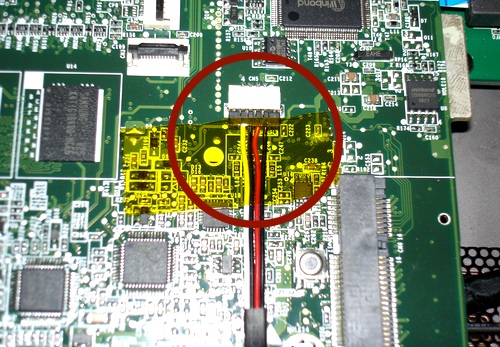
12. Lift the tape holding this cable down - the wires connect the AA1's speakers to the motherboard - and gently pull out the connector. Use the nails on your two index fingers to pull the connector forward and out. Don't just pull the wires.